Apt37's Sophisticated Cloud-Usb Hybrid Attack Campaign Exposed
In a recent discovery, cybersecurity researchers at Zscaler ThreatLabz revealed a sophisticated cloud-USB hybrid attack campaign led by the notorious North Korean group APT37, also known as ScarCruft or Reaper. Dubbed the Ruby Jumper campaign, this malicious operation utilized a combination of cloud storage services and USB-based implants to breach air-gapped networks.
The attack begins with a malicious LNK file that runs PowerShell and extracts hidden payloads, ultimately loading a backdoor called RESTLEAF in memory. RESTLEAF abuses Zoho WorkDrive for command-and-control, authenticating with hardcoded tokens and downloading shellcode for execution via process injection. The shellcode deploys SNAKEDROPPER, which installs a rogue Ruby runtime disguised as a USB utility, establishes persistence, and drops additional components.
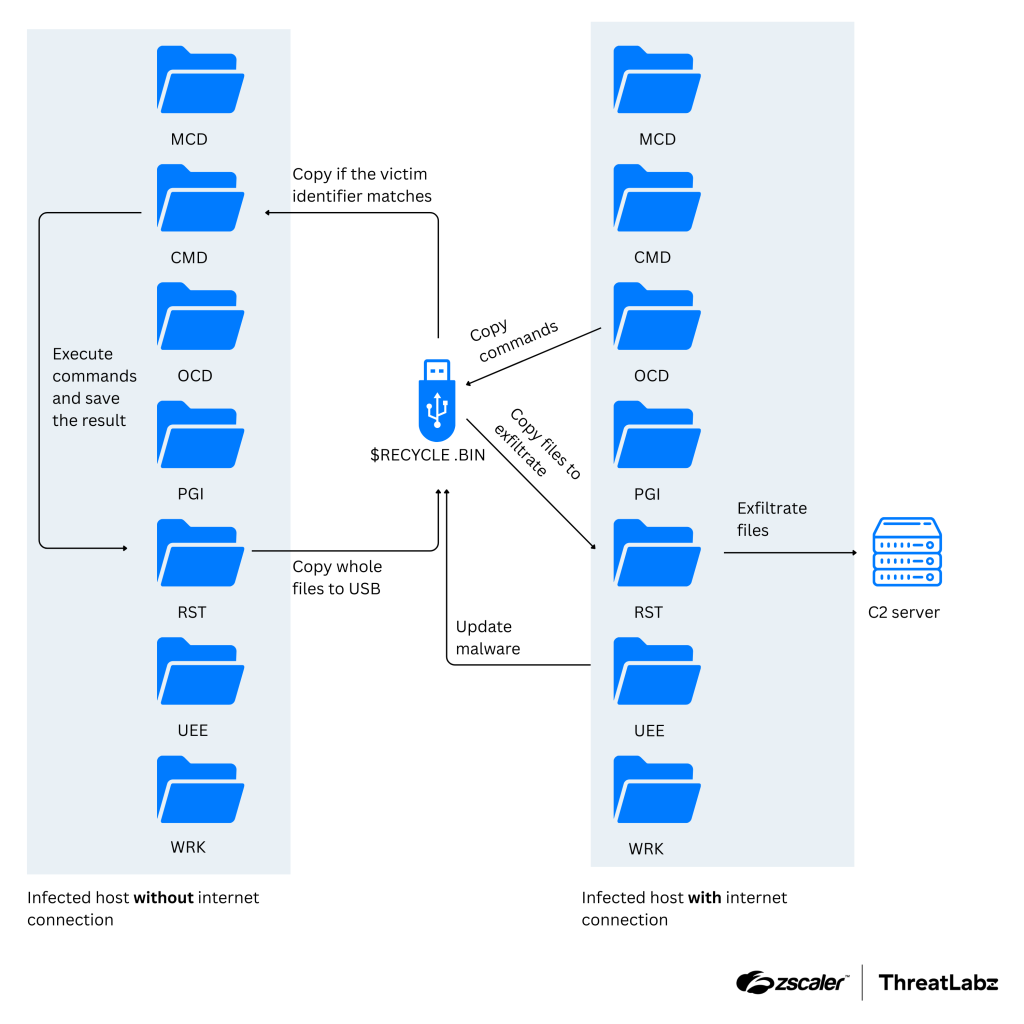
Among the tools used in this campaign is THUMBSBD, a backdoor designed to bridge air-gapped networks using removable media. It collects system data, stages files for exfiltration, and uses hidden folders on USB drives to pass commands and stolen data between isolated systems. The THUMBSBD threat was observed collecting system information including hardware diagnostics (dxdiag), running processes, network configuration (ipconfig /all), recursive file system enumeration (complete file tree), and connectivity status via ping tests and netstat.
Later-stage payloads include FOOTWINE, a surveillance backdoor with keylogging and audio/video capture capabilities, and BLUELIGHT, which leverages cloud services for covert C2 communications. The tools form a sophisticated toolkit for espionage and air-gap compromise, allowing APT37 to access sensitive information from protected networks.
The Ruby Jumper campaign is attributed to APT37 with high confidence by ThreatLabz, citing the group's past activity and tactics. The decoy content used in this attack fits APT37's typical DPRK-focused targeting, which has been observed since at least 2012. This latest discovery highlights the evolving nature of cyber threats and emphasizes the need for robust security measures to counter such attacks.
To maintain a strong security posture, organizations should focus on monitoring endpoint activity and physical access points to counter this threat and other campaigns led by APT37. By being aware of these tactics and adapting their defenses accordingly, individuals and organizations can reduce the risk of falling prey to sophisticated cloud-USB hybrid attacks like the Ruby Jumper campaign.
**Key Takeaways:**
* APT37 combined cloud storage and USB implants to infiltrate air-gapped systems * The group used Zoho WorkDrive for command-and-control and a USB-based implant to breach air-gapped networks in the Ruby Jumper campaign * THUMBSBD, a backdoor designed to bridge air-gapped networks using removable media, was observed collecting system data and staging files for exfiltration * The attack campaign utilized legitimate cloud providers like Google Drive, Microsoft OneDrive, pCloud, and BackBlaze for covert C2 communications * Organizations should focus on monitoring endpoint activity and physical access points to counter this threat and other campaigns led by APT37