Lazarus APT Group Deploys Medusa Ransomware against Middle East Target
The Lazarus APT group, linked to North Korea, has been spotted deploying the Medusa ransomware in an attack on a target in the Middle East. This marks another instance of the group's expanding involvement in ransomware-driven extortion.
According to researchers from Symantec and Carbon Black Threat Hunter Team, North Korea has long been associated with various ransomware families, including Maui and Play. However, the use of Medusa, a ransomware-as-a-service launched in 2023, indicates a shift towards more financially motivated intrusions. This report highlights the Lazarus group's continued involvement in cybercrime, despite charges and a $10 million reward.
The Medusa Ransomware: A Tool for Extortion
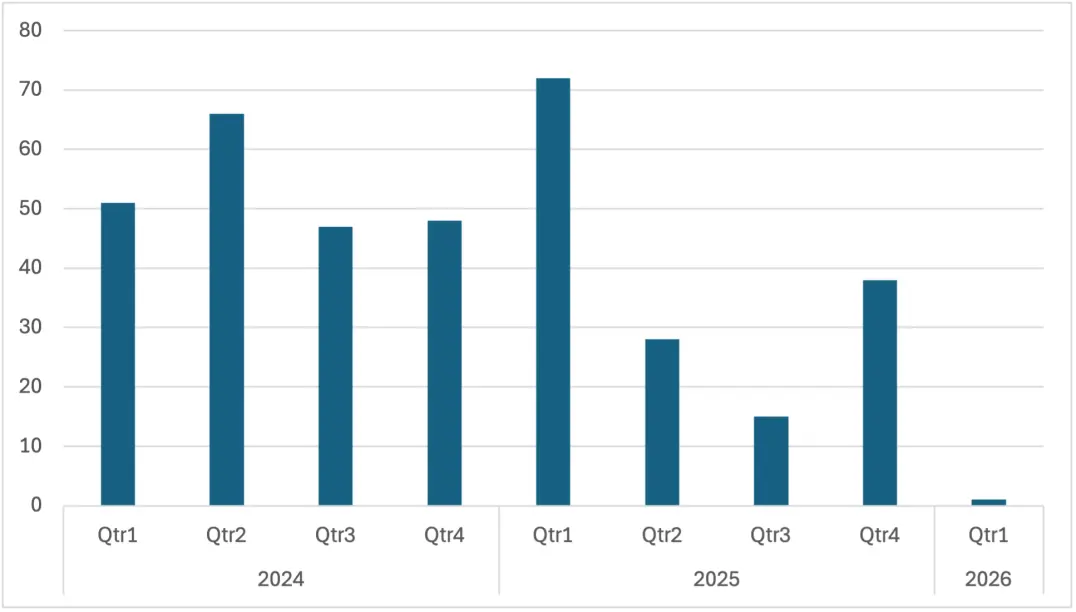
Medusa is a ransomware-as-a-service that allows affiliates to deploy the malware in exchange for a share of ransom payments. It has been linked to over 366 claimed attacks since its launch in 2023. The leak site has listed four U.S. healthcare and non-profit victims, including a mental health nonprofit and a school for autistic children, with average ransom demands reaching $260,000.
The Lazarus Group's Evolving Threat Landscape
North Korea's Lazarus subgroup Stonefly (aka Andariel) has shifted from traditional espionage to ransomware-driven extortion in recent years. Its role became public in July 2025, when U.S. authorities indicted alleged member Rim Jong Hyok over attacks on American hospitals. Prosecutors said ransomware proceeds funded espionage targeting defense, tech, and government sectors in the U.S., Taiwan, and South Korea.
Despite charges and a $10 million reward, activity continued, including financially motivated intrusions in 2024 and reported collaboration with the Play ransomware group. The Lazarus group's toolset now includes Comebacker, Blindingcan, ChromeStealer, Mimikatz, and other custom malware.
Indicators of Compromise (IoCs) and Future Threats
The report provides Indicators of Compromise (IoCs) for the Medusa ransomware attacks. While it remains unclear which subgroup is responsible for the deployment of Medusa in current campaigns, the toolset overlaps with groups like Pompilus.
“The switch to Medusa demonstrates that North Korea’s rapacious involvement in cybercrime continues unabated,” concludes the report. “North Korean actors appear to have few scruples about targeting organizations in the U.S. While some cybercrime outfits claim to steer clear of targeting healthcare organizations due to the reputational damage it may attract, Lazaurs doesn’t seem to be in any way constrained.”
In conclusion, the Lazarus APT group's deployment of Medusa ransomware against a Middle East target highlights the ongoing threat posed by North Korea-linked actors. As the landscape of cybercrime continues to evolve, it is essential for organizations to remain vigilant and implement robust security measures to protect themselves from financially motivated intrusions.
Keywords: Cybersecurity, hacking, data breach, malware, vulnerability, Medusa ransomware, Lazarus APT group, North Korea, cybersecurity threats.