PromptSpy Abuses Gemini AI to Gain Persistent Access on Android Devices
In a significant breakthrough, security researchers at ESET have uncovered PromptSpy, the first known Android malware to exploit Google's Gemini AI to maintain persistence. This malicious app has been spreading rapidly across Android devices, particularly in Argentina, and poses a concerning threat to mobile users.
PromptSpy leverages the powerful capabilities of Gemini AI to adapt to different devices and Android versions, allowing it to evade detection methods more effectively. The malware can capture lockscreen data, block uninstallation attempts, collect device information, take screenshots, and record screen activity as video. This evolution in AI-assisted mobile threats highlights the growing threat landscape of cyber attacks.
The use of Gemini AI by PromptSpy enables the malware to analyze the current screen and receive step-by-step instructions on how to ensure its persistence. The AI model and prompt are predefined in the code and cannot be changed, allowing the malware to adapt to more or less any device, layout, or OS version. This makes it a challenging threat to detect and remove.
According to the report published by ESET, PromptSpy deploys a VNC module for remote control, abuses Accessibility Services to block removal, captures lockscreen data, records video, and uses encrypted C2 communications. The campaign appears to be driven by financial gain and primarily targets users in Argentina. The malware was likely developed in a Chinese-speaking environment and is spread through a dedicated website rather than Google Play.
PromptSpy's use of Gemini AI is a clever tactic that allows it to stay persistent without relying on fixed screen taps or coordinates, which often fail across different Android versions and device layouts. Instead, the malware sends a text prompt plus an XML dump of the current screen to Gemini, giving the AI a full view of buttons, text, and positions. Gemini then replies with JSON instructions telling the malware where to tap.
This approach enables PromptSpy to repeatedly send and receive prompts until the app is successfully locked in the recent apps list, preventing easy removal. The ESET researchers have discovered that the threat evolved from an earlier variant called VNCSpy, with samples uploaded from Hong Kong and later Argentina, suggesting regional targeting.
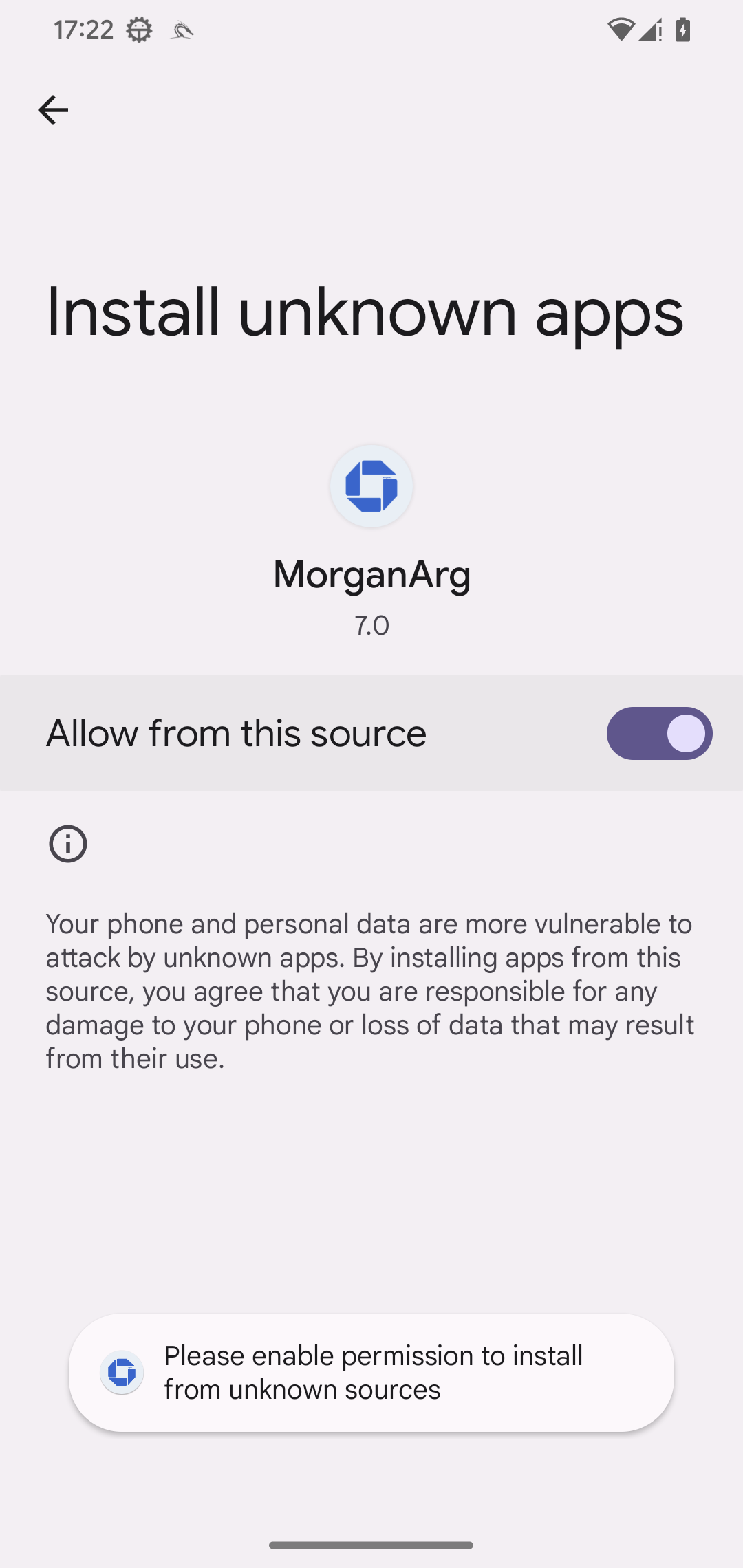
The malware is distributed through malicious websites impersonating Chase Bank, using branding like "MorganArg." A related phishing app, likely from the same actor, helps deliver the final payload. Once installed, PromptSpy abuses Accessibility Services and includes a VNC module, giving attackers full remote control of the device.
It can see the screen, perform gestures, and maintain control while staying hidden in the recent apps list. The analysis of the malicious code revealed debug strings in simplified Chinese, along with functions handling Chinese Accessibility event types, which further suggests that the malware was developed in a Chinese-speaking environment.
PromptSpy is delivered through a dropper that installs a hidden payload APK. After installation, it requests Accessibility permissions, shows a fake loading screen, and secretly contacts Gemini AI to lock itself in the Recent Apps list for persistence. It continuously sends screen data to Gemini and executes returned tap or swipe instructions.
The malware includes a VNC module for full remote control and communicates with its C2 server using AES-encrypted VNC traffic. It can steal PINs, record screens, take screenshots, and list installed apps. To prevent removal, it overlays invisible elements over uninstall buttons. Victims must reboot into Safe Mode to remove it.
PromptSpy marks a concerning evolution in Android malware, showcasing the growing threat landscape of AI-assisted mobile threats. By using generative AI to read and interpret on-screen elements, it can adapt to almost any device or interface, making its persistence more resilient to UI changes.
This campaign highlights how quickly attackers are beginning to misuse AI tools to improve impact, as ESET concludes. PromptSpy is an early example of generative AI-powered Android malware, demonstrating the need for continued awareness and vigilance among mobile users.
Stay informed about emerging threats in the cybersecurity world by following us on Twitter: @securityaffairs, Facebook, and Mastodon.