**H1** Payload Ransomware Strikes Again: Royal Bahrain Hospital Breached in Devastating Data Heist
**Introduction**
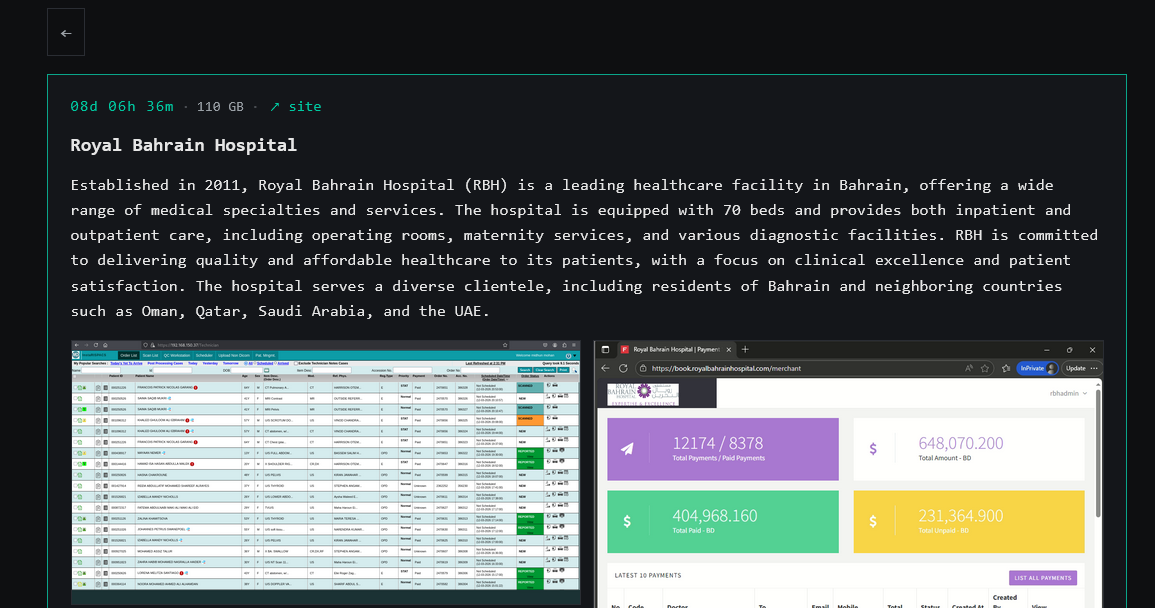
In a shocking turn of events, the Payload Ransomware group has claimed responsibility for breaching the Royal Bahrain Hospital (RBH), a leading healthcare facility in Bahrain. The cybercrime operation, which uses a double-extortion model to pressure victims, has allegedly stolen 110 GB of sensitive data from the hospital's systems. If the ransom is not paid by March 23, the group threatens to release the stolen data, exposing the sensitive information of thousands of patients.
**The Royal Bahrain Hospital: A Target of Opportunity**
The Royal Bahrain Hospital, founded in 2011, is a 70-bed healthcare facility offering a range of services, including surgery, maternity care, and diagnostics. The hospital serves patients from Bahrain and neighboring countries, making it a significant target for cybercriminals. The Payload Ransomware group, which has targeted mid- to large-size companies in emerging markets, has likely chosen the RBH due to its size and reputation in the region.
**Understanding Payload Ransomware: A Growing Threat**
Payload ransomware is a relatively new cybercrime operation that uses a double-extortion model to pressure victims. This means that the group not only encrypts files but also steals sensitive data, which is then published on a Tor leak site if the ransom is not paid. The group's technical capabilities are impressive, using ChaCha20 for file encryption and Curve25519 for key exchange. The ransomware also deletes shadow copies and disables security tools, making it a particularly insidious threat.
**The Double-Extortion Model: A Powerful Tool for Cybercriminals**
The double-extortion model used by Payload ransomware is a powerful tool for cybercriminals. By combining data theft and file encryption, the group can pressure victims to pay the ransom, even if they have backups in place. This approach also allows the group to sell stolen data on the dark web, generating additional revenue. The use of a Tor leak site to publish data from non-paying victims further demonstrates the group's sophistication and willingness to use advanced tactics.
**Conclusion**
The breach of the Royal Bahrain Hospital by the Payload Ransomware group is a stark reminder of the growing threat of cybercrime in the healthcare sector. As hospitals and healthcare facilities increasingly rely on digital systems to store sensitive patient data, they must also invest in robust cybersecurity measures to prevent such attacks. The use of advanced encryption techniques and the double-extortion model by Payload ransomware makes it a particularly insidious threat, and healthcare organizations must be vigilant in protecting themselves against this type of attack.
**Recommendations for Healthcare Organizations**
To prevent similar breaches, healthcare organizations should take the following steps:
* Implement robust cybersecurity measures, including regular software updates and backups * Use advanced encryption techniques to protect sensitive data * Conduct regular security audits and penetration testing * Educate staff on cybersecurity best practices and the importance of data protection * Consider investing in advanced threat detection and response tools
By taking these steps, healthcare organizations can reduce their risk of falling victim to cybercrime and protect the sensitive data of their patients.