Coruna iOS Exploit Kit Targets iPhones Running iOS 13-17.2.1
In a recent discovery by Google's Threat Intelligence Group, a powerful new iOS exploit kit called Coruna (also known as CryptoWaters) has been identified, targeting Apple iPhones running iOS versions 13.0 through 17.2.1. This kit includes five full exploit chains and a total of 23 exploits, making it a highly capable tool against iPhones running these older versions of the operating system.
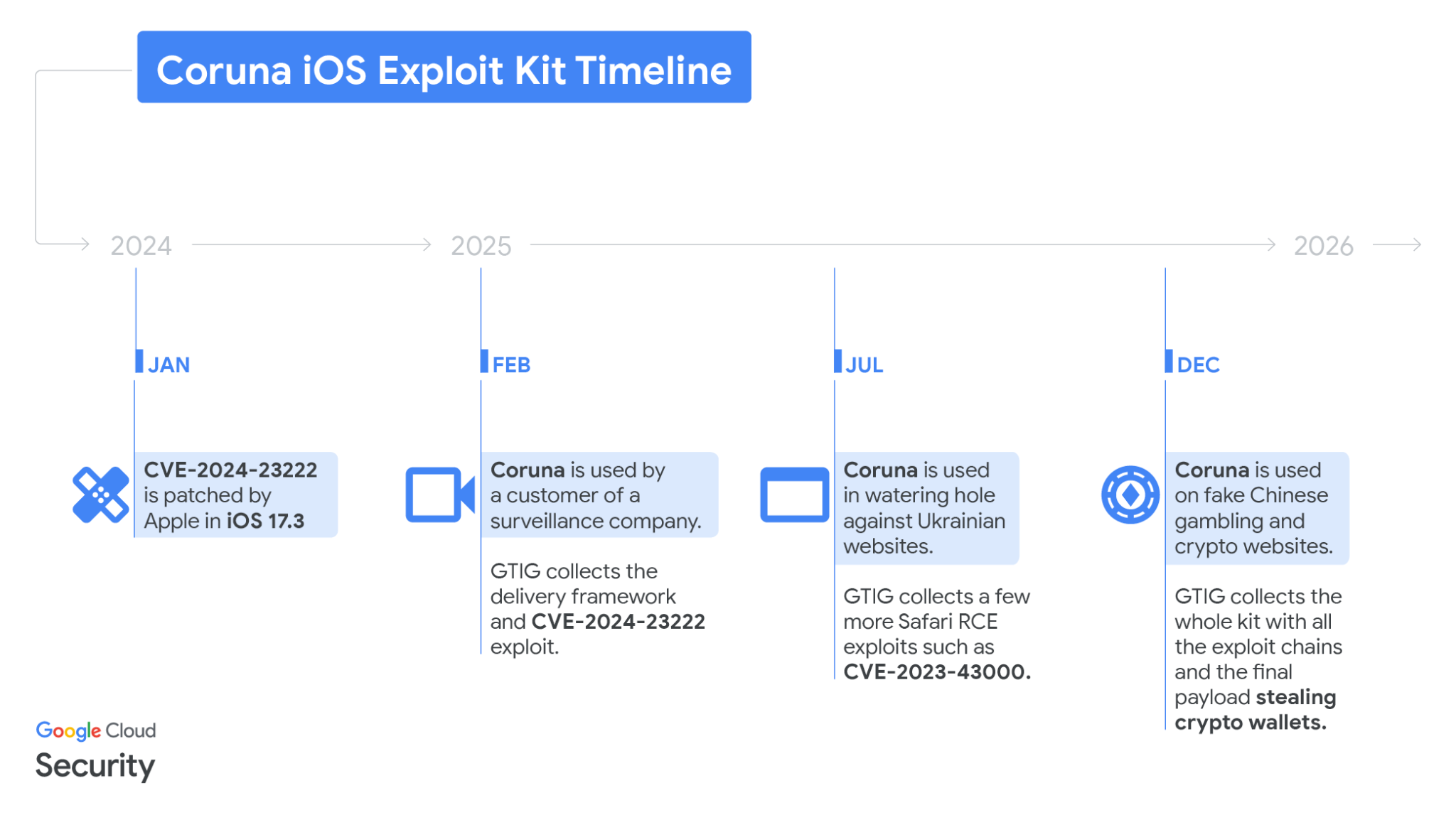
The Coruna iOS Exploit Kit was first detected in February 2025 by GTIG, who captured parts of an iOS exploit chain used by a customer of a surveillance company. The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits, with the most advanced ones using non-public exploitation techniques and mitigation bypasses.
How Does the Coruna Exploit Kit Work?
The framework uses fingerprinting to detect device type and iOS version, then loads the appropriate WebKit RCE exploit and pointer authentication bypass. One recovered exploit, CVE-2024-23222, was later patched in iOS 17.3.
Exploits Used by Coruna
Coruna includes 23 exploits covering iOS 13 through 17.2.1, with advanced mitigation bypasses and reusable modules for defeating memory and kernel protections. The kit also embeds reusable modules to ease the exploitation of vulnerabilities used as zero-days in Operation Triangulation.
Exploitation Chain
At the end of the chain, a stager called PlasmaLoader injects into a root daemon and deploys a financially focused payload. This payload can decode QR codes from images on disk, analyze blobs of text to look for specific keywords like "backup phrase" or "bank account," and exfiltrate sensitive information.
Attackers Using Coruna
Google tracked the use of the exploit in highly targeted attacks by a surveillance vendor's customer, Ukrainian watering hole campaigns by UNC6353, and later in broad-scale attacks by Chinese financial threat actor UNC6691. The active market for "second-hand" zero-day exploits has led to multiple threat actors reusing and adapting these advanced techniques for new vulnerabilities.
Conclusion
The Coruna iOS Exploit Kit highlights the ongoing threat of advanced mobile malware and the importance of staying up-to-date with the latest security patches. Google's Threat Intelligence Group shared the findings to raise awareness and protect users, adding identified domains to Safe Browsing. With this new information, it is essential for users to be vigilant and take steps to secure their devices against such threats.
Key Takeaways:
* Coruna iOS Exploit Kit targets iPhones running iOS 13-17.2.1 * The kit includes five full exploit chains and a total of 23 exploits * Advanced exploitation techniques and mitigation bypasses are used by the kit * The kit is ineffective against the latest iOS release