900 Sangoma FreePBX Instances Infected with Web Shells After CVE-2025-64328 Exploit
In the past few months, a massive cyberattack has affected hundreds of Sangoma FreePBX systems worldwide. The attack exploited a command injection flaw in the endpoint manager interface, allowing attackers to execute malicious commands and maintain persistent access to compromised systems. In this article, we'll delve into the details of the CVE-2025-64328 vulnerability and its impact on 900 Sangoma FreePBX instances.
The campaign that began in early December exploited a post-authentication command injection vulnerability, tracked as CVE-2025-64328 (CVSS score of 8.6), in the endpoint manager interface of Sangoma FreePBX systems. This allowed attackers to execute malicious commands and maintain persistent access to compromised systems. The vulnerability is fixed in version 17.0.3, but hundreds of affected systems are still running web shells, likely due to exploitation of CVE-2025-64328.
The Shadowserver Foundation reports that around 900 FreePBX instances are still compromised and running web shells, with about 400 affected systems located in the United States, and dozens more in countries including Brazil, Canada, Germany, France, the UK, Italy, and the Netherlands. The Canadian Centre for Cyber Security ( @cybercentre_ca) has provided more comprehensive information on FreePBX instances running webshells, with over 900 IPs seen compromised.
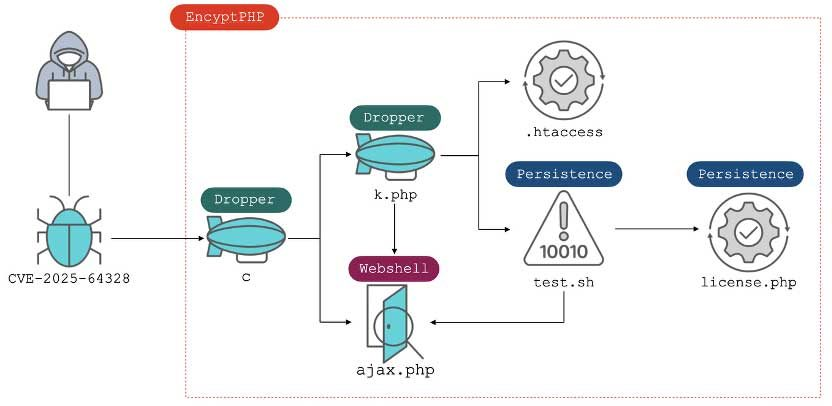
Researchers have identified a new web shell dubbed "EncystPHP," capable of remote command execution, persistence, and further web shell deployment. The attacks were linked to the threat group INJ3CTOR3, known for targeting past vulnerabilities in FreePBX and Elastix systems. The campaign follows a familiar pattern: exploiting a flaw and installing a PHP web shell to maintain access.
The attackers delivered the EncystPHP dropper from an IP address 45[.]234[.]176[.]202, which resolves to the domain crm[.]razatelefonia[.]pro. Once installed, the malware locked key files, harvested database configs, deleted cron jobs and user accounts, and removed rival web shells. It created a root-level user, reset passwords, injected an SSH key, and ensured port 22 stayed open for persistent access.
The dropper also fetched additional payloads, erased logs, removed the Endpoint Manager module, restored permissions to avoid detection, and deployed Base64-encoded web shells to maintain long-term control. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the flaw in Sangoma FreePBX to its Known Exploited Vulnerabilities (KEV) catalog in early February.
To protect your Sangoma FreePBX system from this vulnerability, we recommend updating to version 17.0.3 or higher. Additionally, ensure that all software is up-to-date and consider implementing additional security measures, such as using a web application firewall (WAF) or intrusion detection/prevention systems.
In conclusion, the CVE-2025-64328 exploit has had a significant impact on hundreds of Sangoma FreePBX instances worldwide. It's essential to stay informed about known vulnerabilities and take proactive steps to protect your systems from exploitation.
**Key Takeaways:**
* CVE-2025-64328 is a post-authentication command injection vulnerability in the endpoint manager interface of Sangoma FreePBX systems. * The vulnerability has affected around 900 Sangoma FreePBX instances worldwide, with hundreds still running web shells. * The attacks were linked to the threat group INJ3CTOR3 and used a PHP web shell dubbed "EncystPHP" for remote command execution and persistence. * Updating to version 17.0.3 or higher is recommended to patch the vulnerability.
**Additional Resources:**
* CVE-2025-64328 advisory * FreePBX endpoint manager interface vulnerability * Shadowserver Foundation's vulnerability report * Fortinet's analysis on the EncystPHP web shell