Salesloft Breach Compromises 'Numerous' Salesforce Environments
Updated: August 27, 2025 15:23 EDT
A recent security breach has left numerous Salesforce environments vulnerable to hacking. Salesloft Inc., a popular cloud platform used by over 5,000 companies, disclosed the breach last Thursday. The breach is attributed to a sophisticated attack that utilized a chatbot developed by Salesloft itself.
The search giant Google LLC determined that the threat actor behind the hacking campaign, tracked as UNC6395, downloaded "large volumes of data from numerous corporate Salesforce instances." This attack highlights the risks associated with using third-party tools and services in business environments.
About Drift and OAuth
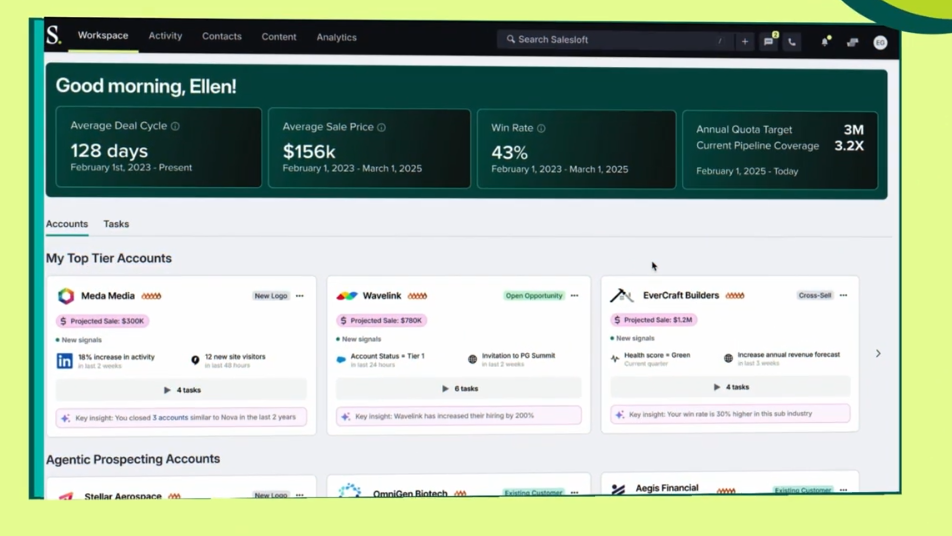
Drift is a chatbot component of Salesloft's platform that can field questions from potential customers visiting a company's website, estimate the likelihood of a purchase, and sync information provided by prospects to a company's Salesforce environment. Drift includes a connector that integrates with Salesforce using OAuth technology.
OAuth Credentials Compromised
The hackers gained access to Salesloft's OAuth credentials and used them to access customers' Salesforce environments. This breach demonstrates the importance of robust security measures, particularly in the use of OAuth for establishing connections between applications and services.
Impact on Affected Organizations
Customers who don't use the company's Drift chatbot were not affected by this breach. However, those that do, must now take steps to secure their Salesforce environments. According to Google researchers, the hackers used requests written in SOQL query language to extract sensitive data, including Amazon Web Services access keys, passwords, and Snowflake-related access tokens.
The hackers attempted to hide their tracks by using IP addresses associated with popular cloud platforms to process malicious network requests and camouflaged the traffic using Tor. They also deleted files that contained information about the queries they ran in customer environments, although logs were not impacted and organizations should review relevant logs for evidence of data exposure.
Timeline of Events
The hacking campaign is believed to have started on August 8 and continued until "at least" last Monday. Salesloft has since shut down the vulnerable OAuth connections that linked Drift to customers' Salesforce environments and released multiple indicators of compromise, which are data points about the hacking campaign that companies can use to determine if they were affected.
What Organizations Need to Do
"Impacted organizations should search for sensitive information and secrets contained within Salesforce objects and take appropriate action," warned Google's researchers. This includes revoking API keys, rotating credentials, and performing further investigation into the breach.
Salesloft Breach: A Reminder of Cybersecurity Risks
The recent Salesloft breach underscores the need for robust cybersecurity measures in business environments. As companies continue to rely on cloud-based services and third-party tools, it is essential that they prioritize security awareness and take proactive steps to protect their data.