China Linked Silk Typhoon Targeted Diplomats by Hijacking Web Traffic
In a recent alert issued by Google's Threat Intelligence Group (GTIG), a China-linked cyber espionage group known as UNC6384 has been identified as behind a sophisticated attack targeting diplomats in Southeast Asia and globally. The attack, which was detected in March 2025, utilized an advanced adversary-in-the-middle (AitM) technique to hijack web traffic and redirect it to a website that delivered malware.
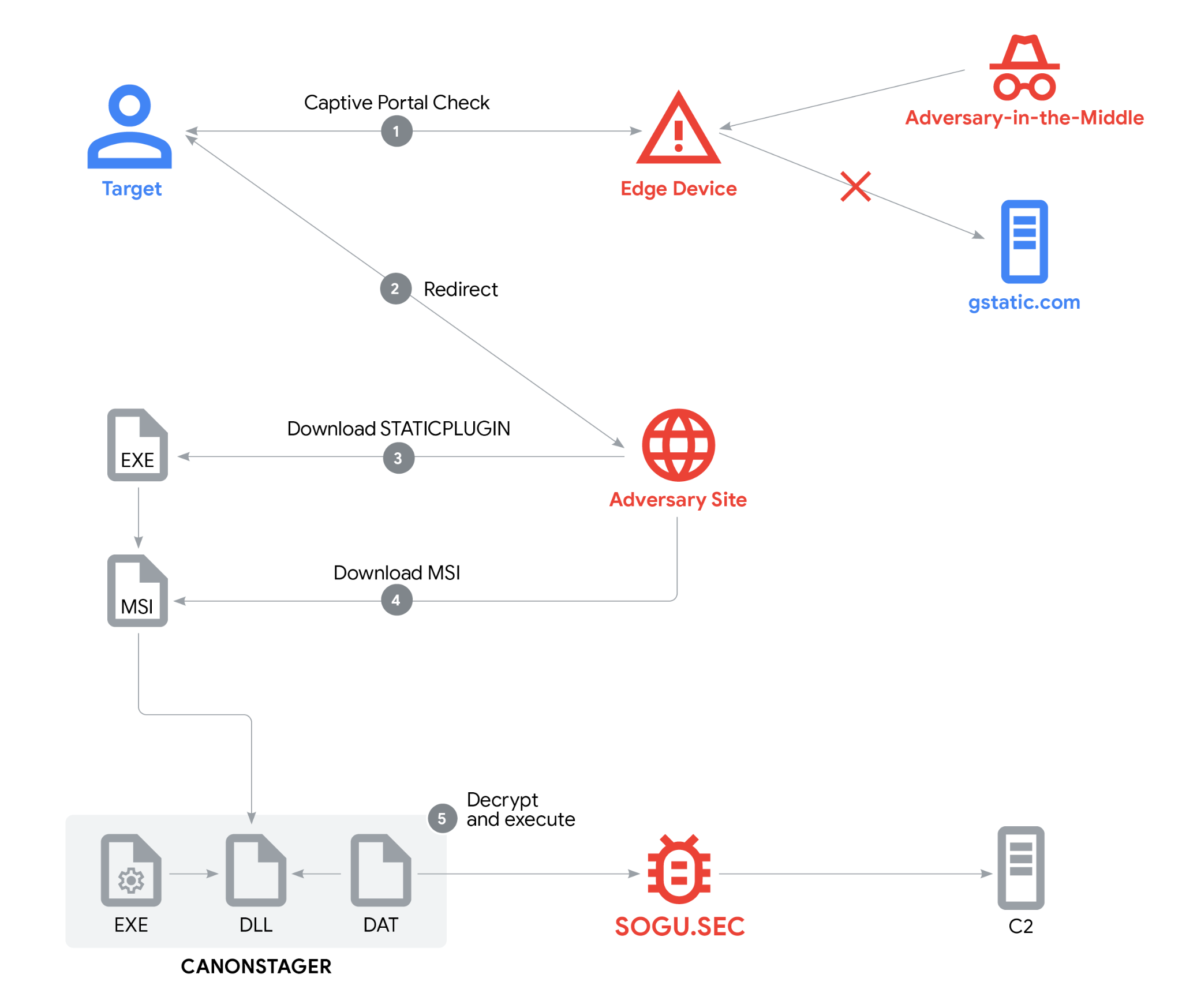
The attackers, linked to the Chinese threat actor TEMP.Hex, also known as Mustang Panda, employed a complex tactic known as captive portal redirection. This involved hijacking a network's captive portal, which is a network setup that directs users to a specific webpage, usually a login or splash page, before granting internet access. The attack was disguised as an Adobe Plugin update, and the attackers used HTTPS and a valid TLS certificate to make the site appear legitimate.
The attackers tricked targets into downloading malware by displaying a blank landing page with an "Install Missing Plugins..." button. When clicked, JavaScript triggered the download of "AdobePlugins.exe," while showing a background image with execution instructions. However, the fake installer ran without actually installing any plugins, and instead, it launched a multi-stage chain designed to evade defenses and remain stealthy.
The malware, which was delivered via the signed downloader (STATICPLUGIN), installed the PlugX backdoor (SOGU.SEC) on infected systems. The SOGU.SEC backdoor allowed the attackers to bypass Windows security and maintain communication with their command-and-control server.
"A captive portal is a network setup that directs users to a specific webpage, usually a login or splash page, before granting internet access," states the GTIG's report. "While 'gstatic.com' is a legitimate domain, our investigation uncovered redirect chains from this domain leading to the threat actor's landing webpage and subsequent malware delivery, indicating an AitM attack."
The attackers leveraged legitimate Windows features and digitally signed binaries to appear credible and avoid detection. The use of advanced evasion techniques, including API hashing, Thread Local Storage (TLS) for storing function addresses, and indirect code execution via Windows message queues and hidden window procedures, allowed the SOGU.SEC backdoor to decrypt and run without leaving artifacts on the disk.
"This campaign is a clear example of the continued evolution of UNC6384's operational capabilities and highlights the sophistication of PRC-nexus threat actors," concludes the report. "The use of advanced techniques such as AitM combined with valid code signing and layered social engineering demonstrates this threat actor's capabilities."
The attack follows a broader trend observed by GTIG of PRC-nexus threat actors increasingly employing stealthy tactics to avoid detection. Google has published indicators of compromise (IoCs) and YARA rules for detecting malware employed in the attacks.
Stay safe online by following the latest security news and alerts from trusted sources like GTIG. Follow me on Twitter: @securityaffairs, Facebook, and Mastodon for the latest updates.