Android.Backdoor.916.origin Malware Targets Russian Business Executives
A new Android spyware, dubbed Android.Backdoor.916.origin, has been discovered to target business executives in Russia. The malware is disguised as an antivirus program linked to Russia's intelligence agency, FSB, and is designed to execute attacker commands, enabling surveillance, keylogging, and theft of sensitive data.
Researchers at Doctor Web first observed the malicious software in January 2025, but since its discovery, they have been monitoring its evolution and identifying multiple versions. The experts speculate that Android.Backdoor.916.origin was specifically designed to be used in targeted attacks against representatives of Russian businesses.
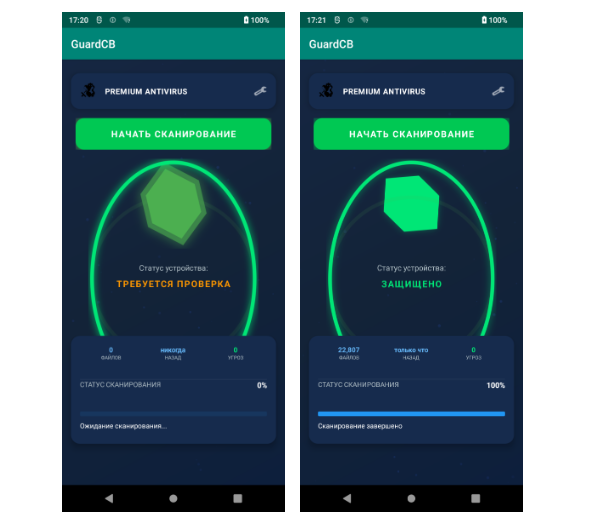
The malware is distributed via private messages in messengers under the guise of an antivirus called "GuardCB". The application has an icon resembling the emblem of the Central Bank of the Russian Federation, and its interface provides only one language – Russian. This suggests that the malicious program is entirely focused on Russian users.
The fake antivirus app mimics real security tools to avoid removal, running simulated scans with random fake detections. On installation, it requests dangerous permissions, including geolocation, SMS, media, camera, audio, background activity, data deletion, lock screen changes, and Accessibility Service. This gives attackers full control and stealthy persistence on the device.
The malware constantly maintains its services by connecting to a C2 server to steal sensitive information such as SMS, contacts, call logs, geolocation, images, audio/video/screen, execute commands, and send device info. It uses separate ports for each data type.
Android.Backdoor.916.origin exploits the Accessibility Service to keylog and steal data from apps like Telegram, WhatsApp, Gmail, Chrome, and Yandex browsers. The malware also has the ability to self-protect from removal and can work with a large number of control servers, information about which is located in its configuration.
The researchers have identified 15 hosting providers used by the malware, but currently, this functionality is not being utilized. Doctor Web has notified domain registrars of the corresponding violations to prevent further distribution of the malicious software.
Indicators of Compromise
If you suspect that your device may be infected with Android.Backdoor.916.origin, here are some indicators of compromise to look out for:
- Unusual or suspicious behavior on your device
- Random fake detections from the malware's simulated scans
- Permission requests that seem unusual or excessive
- Suspicious activity related to geolocation, SMS, media, camera, audio, or background activity
Stay safe online by regularly scanning your device for malware and being cautious when downloading apps from unknown sources. Follow us on Twitter: @securityaffairs and Facebook, and stay up-to-date with the latest security news and alerts.