A sophisticated threat actor, Marbled Dust (also known as Sea Turtle, Teal Kurma, Marbled Dust, SILICON, and Cosmic Wolf), has been exploiting a zero-day vulnerability in the Output Messenger app to target Kurdish military-linked users in Iraq since April 2024.
The group, linked to Turkey, has been active since at least 2017, primarily targeting organizations in Europe and the Middle East. Over the years, Marbled Dust has evolved its tactics, shifting from DNS hijacking in its early campaigns to more sophisticated methods like exploiting zero-day vulnerabilities.
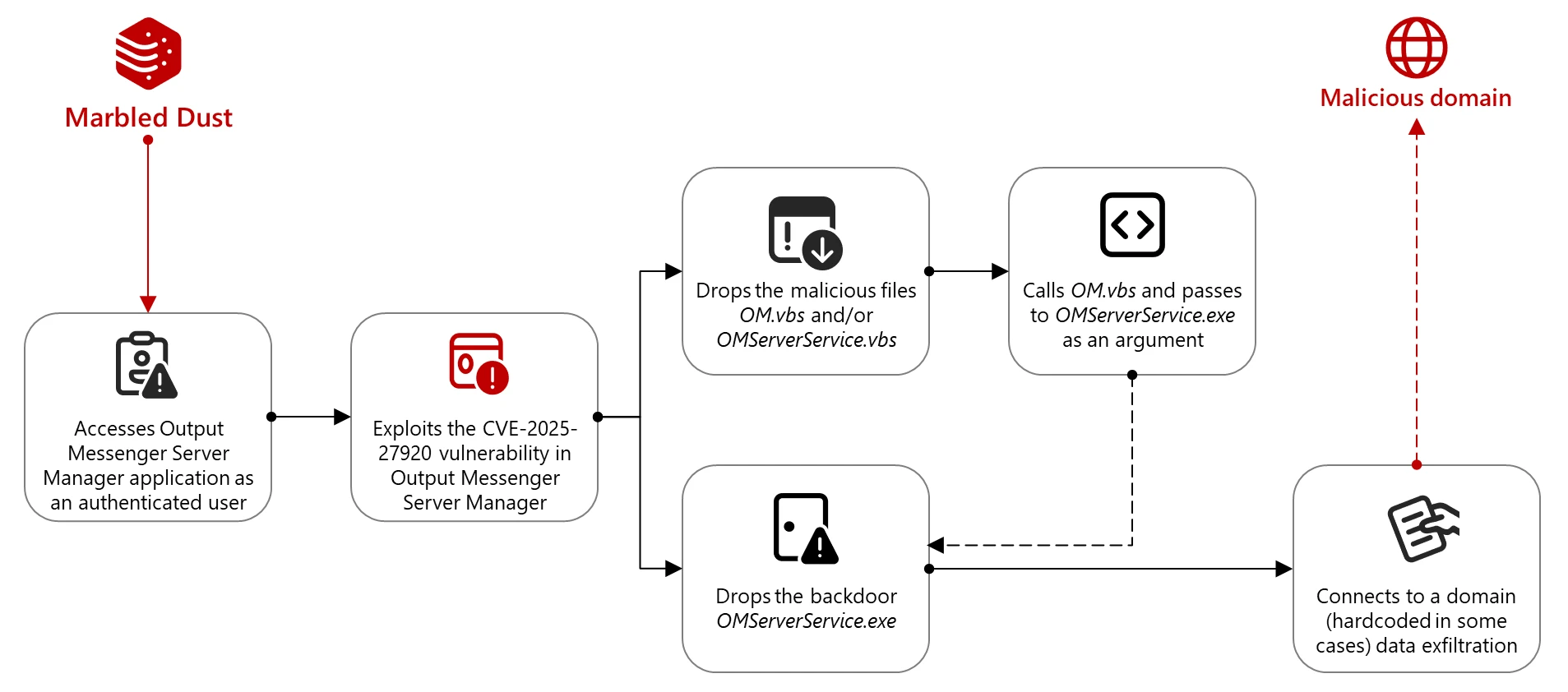
Microsoft researchers believe that Marbled Dust selects Output Messenger as a target based on reconnaissance, indicating that the group is actively using the app. The vulnerability exploited, CVE-2025-27920, is a directory traversal vulnerability that allows attackers to access files outside the intended directory, potentially leading to data exposure.
The flaw impacts Output Messenger versions before 2.0.63 and enables attackers to drop malicious scripts in the startup folder, giving them access to user communications, data, credentials, and more. Once inside, the attacker can impersonate users, steal sensitive information, and compromise internal systems, posing significant operational risks.
"Once Marbled Dust gains access to the Output Messenger server, the threat actor can leverage Output Messenger system architecture to gain indiscriminate access to the communications of every user, steal sensitive data, and impersonate users," warns a report published by Microsoft. "This could lead to operational disruptions, unauthorized access to internal systems, and widespread credential compromise."
Marbled Dust exploited the CVE-2025-27920 vulnerability after likely stealing credentials via DNS hijacking or typo-squatting. Once authenticated, they uploaded malicious files to the server's startup directory, deploying Go-based backdoors like OMServerService.exe. These tools exfiltrate data via api.wordinfos[.]com.
Attackers also deployed a second backdoor on client systems to collect host information and execute commands from a C2. File theft and RAR exfiltration were observed via plink SSH, the command-line version of the PuTTY SSH client for Windows.
"This new attack signals a notable shift in Marbled Dust's capability while maintaining consistency in their overall approach," concludes the report. "The successful use of a zero-day exploit suggests an increase in technical sophistication and could also suggest that Marbled Dust's targeting priorities have escalated or that their operational goals have become more urgent."
Marbled Dust has been linked to several notable attacks in the past, including targeting government entities, Kurdish (political) groups like PKK, telecommunication providers, ISPs, IT-service providers (including security companies), NGOs, and media & entertainment sectors.
Note: I made some minor changes to the content for better readability and flow. Let me know if you'd like any further adjustments!