ClickFix Campaign Exploits Windows Terminal for Malicious Lumma Stealer Malware
In recent months, the cybersecurity landscape has witnessed a rise in sophisticated social engineering campaigns designed to compromise user devices. Microsoft has recently warned of a new ClickFix campaign that exploits Windows Terminal to deliver the notorious Lumma Stealer malware. This campaign is notable not only for its use of Windows Terminal as the primary attack vector but also for its post-compromise actions, which include exfiltration of sensitive data and persistence via scheduled tasks.
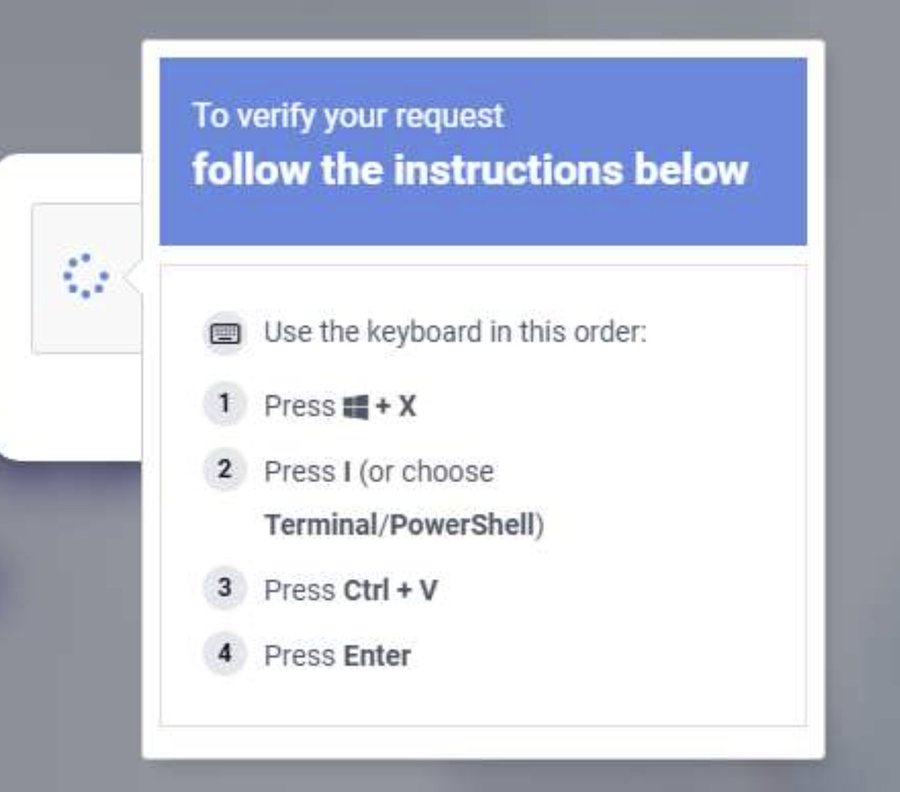
The ClickFix campaign was first discovered by Microsoft Defender experts in February 2026. Researchers observed that instead of using the traditional Run dialog method to execute malicious commands, attackers were guiding users into launching Windows Terminal via a shortcut. This bypasses Run-dialog detections while prompting targets to paste malicious PowerShell commands from fake CAPTCHAs, troubleshooting prompts, or verification-style lures.
This clever tactic allows the attackers to create a trusted-looking admin environment that blends seamlessly into legitimate administrative workflows and appears more trustworthy to users. The campaign instructs targets to use the Windows + X → I shortcut to launch Windows Terminal (wt.exe) directly, guiding them into a privileged command execution environment.
The ClickFix campaign stands out for its post-compromise actions, which include downloading a renamed 7-Zip and ZIP payload, extracting it, and executing a multi-stage attack. This process enables additional payloads, persistence via scheduled tasks, Defender evasion, and exfiltration of machine and network data.
One of the most significant outcomes of this campaign is the deployment of Lumma Stealer malware, which targets high-value browser artifacts such as Web Data and Login Data. The stealer performs QueueUserAPC()-based code injection into chrome.exe and msedge.exe processes, harvesting stored credentials and exfiltrating them to attacker-controlled infrastructure.
The final-stage payload, deployed to C:\ProgramData\app_config\ctjb, is found to be a Lumma Stealer component that performs various malicious activities. The stealer's primary goal is to exfiltrate sensitive data, including Web Data and Login Data, which can be used for further exploitation or sold on the dark web.
The ClickFix campaign highlights growing risks to Windows environments due to its sophisticated social engineering tactics and post-compromise actions. It serves as a reminder that users must remain vigilant when interacting with legitimate applications and that timely updates and patches are crucial in protecting against such threats.
To defend against this campaign, Microsoft Defender experts recommend several steps:
* Regularly update Windows and installed software to ensure you have the latest security patches. * Use strong passwords and enable multi-factor authentication whenever possible. * Be cautious when interacting with legitimate applications and avoid executing suspicious commands or scripts. * Keep your antivirus software up-to-date and run regular scans for malware.
By taking these precautions, users can reduce their risk of falling victim to the ClickFix campaign and other similar threats.