Google GTIG: 90 Zero-Day Flaws Exploited in 2025 as Enterprise Targets Grow
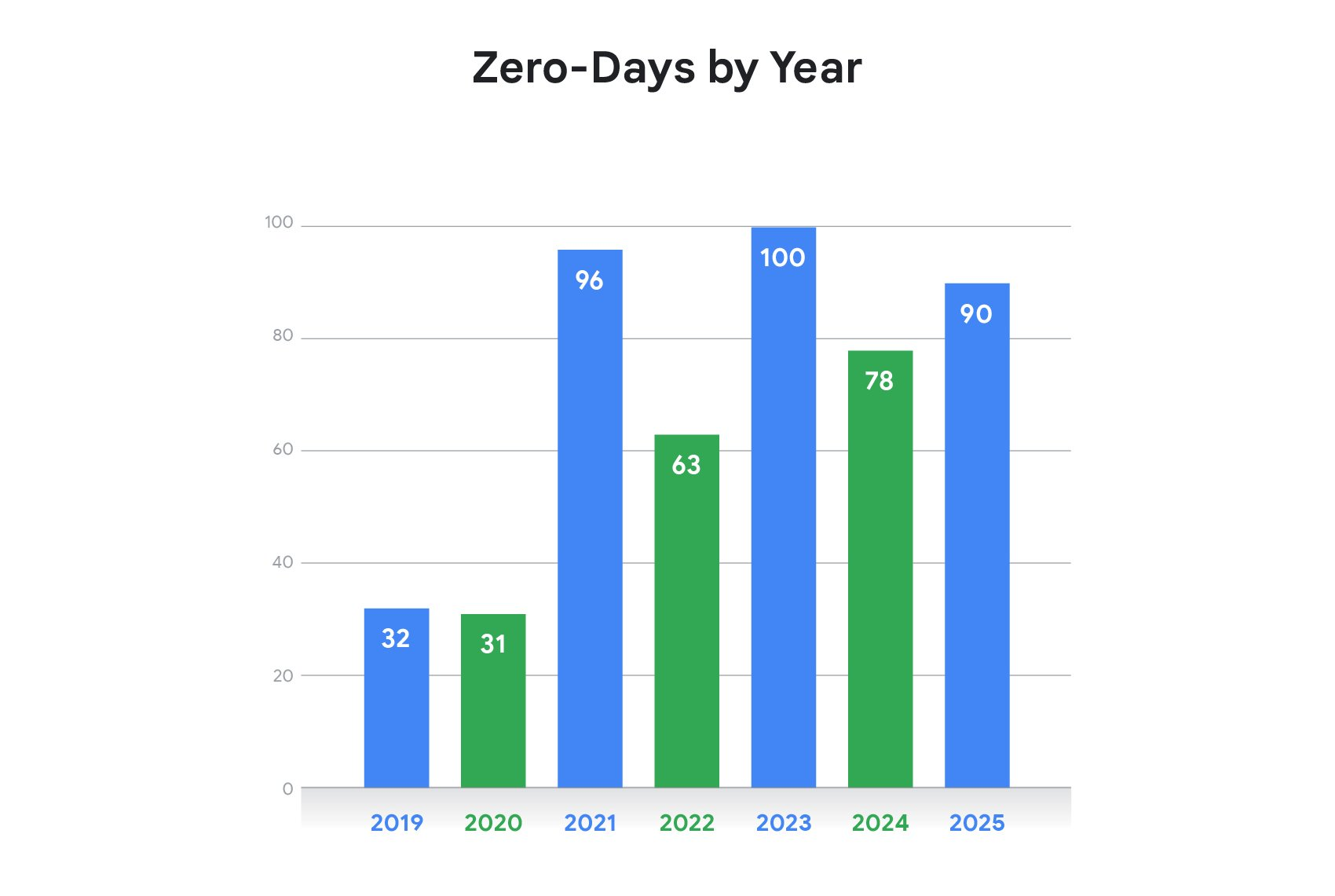
In a stark reminder of the ever-evolving threat landscape, Google's Threat Intelligence Group (GTIG) has reported an alarming rise in zero-day vulnerabilities exploited in 2025. The number of observed zero-days increased to 90, with nearly half targeting enterprise technologies, marking a significant shift toward enterprise-focused attacks. This development highlights the growing importance of cybersecurity awareness and measures for protecting corporate infrastructure.
According to Google's GTIG report, while slightly below the 100 observed in 2023, the number of identified zero-day vulnerabilities increased from 78 in 2024. This upward trend reflects a rising threat landscape where attackers are increasingly targeting edge devices, security appliances, and enterprise systems.
Nation-state actors mainly targeted edge devices and security appliances, while commercial surveillance vendors continued focusing on mobile and browser exploit chains. The report notes that as vendor mitigations evolve and become more effective, threat actors have been forced to expand or adjust their techniques. In some cases, attackers have increased the number of chained vulnerabilities to reach desired levels of access within highly protected components.
Another 47 zero-days (52%) targeted end-user platforms, with operating systems being the most exploited category with 39 flaws. This upward trend reflects the ongoing struggle to protect against zero-day attacks. Mobile OS exploits rose to 15 cases, while browsers accounted for less than 10% of zero-day activity, suggesting improved security hardening.
Most exploited zero-days targeted major tech vendors due to their massive user bases across operating systems, browsers, and mobile platforms. Security and networking companies such as Cisco, Fortinet, Ivanti, and VMware were also frequent targets because of the strategic value of VPNs, virtualization, and edge infrastructure.
Many attacks aimed at remote code execution or privilege escalation, often exploiting injection flaws, memory corruption, or weak access controls. Commercial surveillance vendors (CSVs) were the most active users of zero-day exploits in 2025, surpassing traditional state-sponsored espionage groups for the first time. Firms such as Intellexa continued selling advanced spyware to government clients.
China-linked cyber-espionage groups remained the most prolific among nation-state actors, often targeting edge and networking devices to maintain long-term access. Financially motivated groups also increased zero-day use, including ransomware operations linked to FIN11 and the Clop ransomware group.
Researchers observed sophisticated exploit chains affecting browsers, mobile devices, and enterprise appliances, including attacks on SonicWall systems that combined authentication bypass, remote code execution, and privilege escalation vulnerabilities. The increasing sophistication of these attack chains highlights the ongoing need for robust cybersecurity measures.
The Future of Cybersecurity: Leveraging AI to Strengthen Defenses
Google expects AI use to grow in 2026, and threat actors will leverage it to speed up vulnerability discovery and exploit development. Defenders can use AI to strengthen security operations by identifying unknown flaws early and mitigating them before they are weaponized.
This highlights the importance of staying ahead of emerging threats through proactive cybersecurity measures. By leveraging AI-powered tools and techniques, organizations can enhance their defenses and protect against the ever-evolving threat landscape.