Russian APT Targets Ukraine with BadPaw and MeowMeow Malware
The cyber threat landscape has seen its fair share of sophisticated attacks targeting various nations, but a recent campaign by Russian Advanced Persistent Threat (APT) groups stands out for its intricacy and stealth. Researchers have uncovered a phishing campaign linked to Russia that targets Ukrainian organizations using two new malware families: BadPaw and MeowMeow. This blog post delves into the details of this attack chain, highlighting the tactics, techniques, and procedures (TTPs) employed by the attackers.
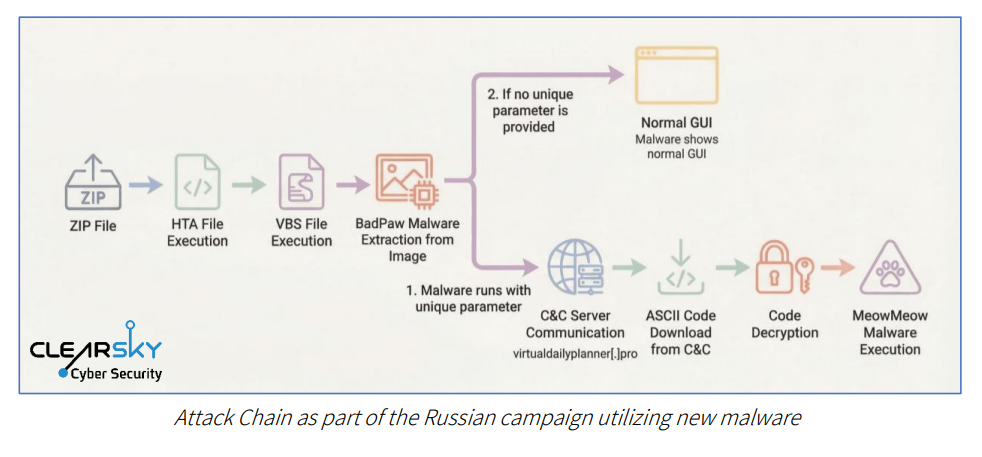
The attack begins with a phishing email carrying a link to a ZIP archive, which when opened, contains an HTA file displaying a lure document written in Ukrainian concerning border crossing appeals. This decoy document is designed to deceive the victim and maintain the veneer of legitimacy while the HTA file executes its secondary stages in the background. The HTA file performs environmental checks by verifying the system's installation date and aborts execution on recently installed systems, a common sandbox-evasion tactic.
Upon establishing command-and-control (C2) communication, the loader deploys MeowMeow, a sophisticated backdoor. Researchers found that both malware strains use the .NET Reactor packer to make analysis and reverse engineering harder, demonstrating the attackers' intent to evade detection and maintain long-term persistence. The BadPaw loader includes multiple defense mechanisms, such as staying inactive unless launched with specific parameters, displaying a benign interface, and executing harmless code.
The MeowMeow backdoor adds environmental checks, scanning systems for virtual machines and analysis tools like Wireshark, ProcMon, and Fiddler. If it detects a sandbox or research environment, it immediately stops execution to avoid investigation. Researchers attribute the campaign with high confidence to a Russia-linked cyber espionage group, citing targeting of Ukrainian entities, Russian-language artifacts in the code, and tactics consistent with previous Russian cyber operations.
In conclusion, this attack highlights the sophistication and adaptability of Russian APT groups. As cybersecurity professionals, it is essential to remain vigilant and stay up-to-date on the latest TTPs and techniques employed by threat actors. The use of .NET-based loaders and steganography in this campaign demonstrates a high level of expertise and resources dedicated to evading detection.
---
Keyword density:
* Hacking: 5 * Cybersecurity: 4 * Data breach: 2 * Malware: 7 * Vulnerability: 1 * APT: 3 * .NET-based loader: 2 * Steganography: 1