# The Great .env File Fiasco: 12 Million Exposed Revealing Widespread Security Failures Across Industries
The world of cybersecurity has been rocked by a recent discovery that exposes the shocking extent of security failures worldwide. Researchers at Mysterium VPN have identified a staggering 12 million IP addresses serving publicly accessible environment files, commonly known as .env files, revealing sensitive credentials and tokens across various industries and regions.
These .env files, designed to store key-value pairs for application configurations, are often overlooked by developers and IT teams alike. The simplicity of the format belies its vulnerability to exposure, allowing attackers to bypass traditional security measures and gain access to valuable information with ease. As a result, organizations are facing a growing threat landscape where database credentials, API keys, JWT signing secrets, cloud tokens, and other sensitive values are being compromised.
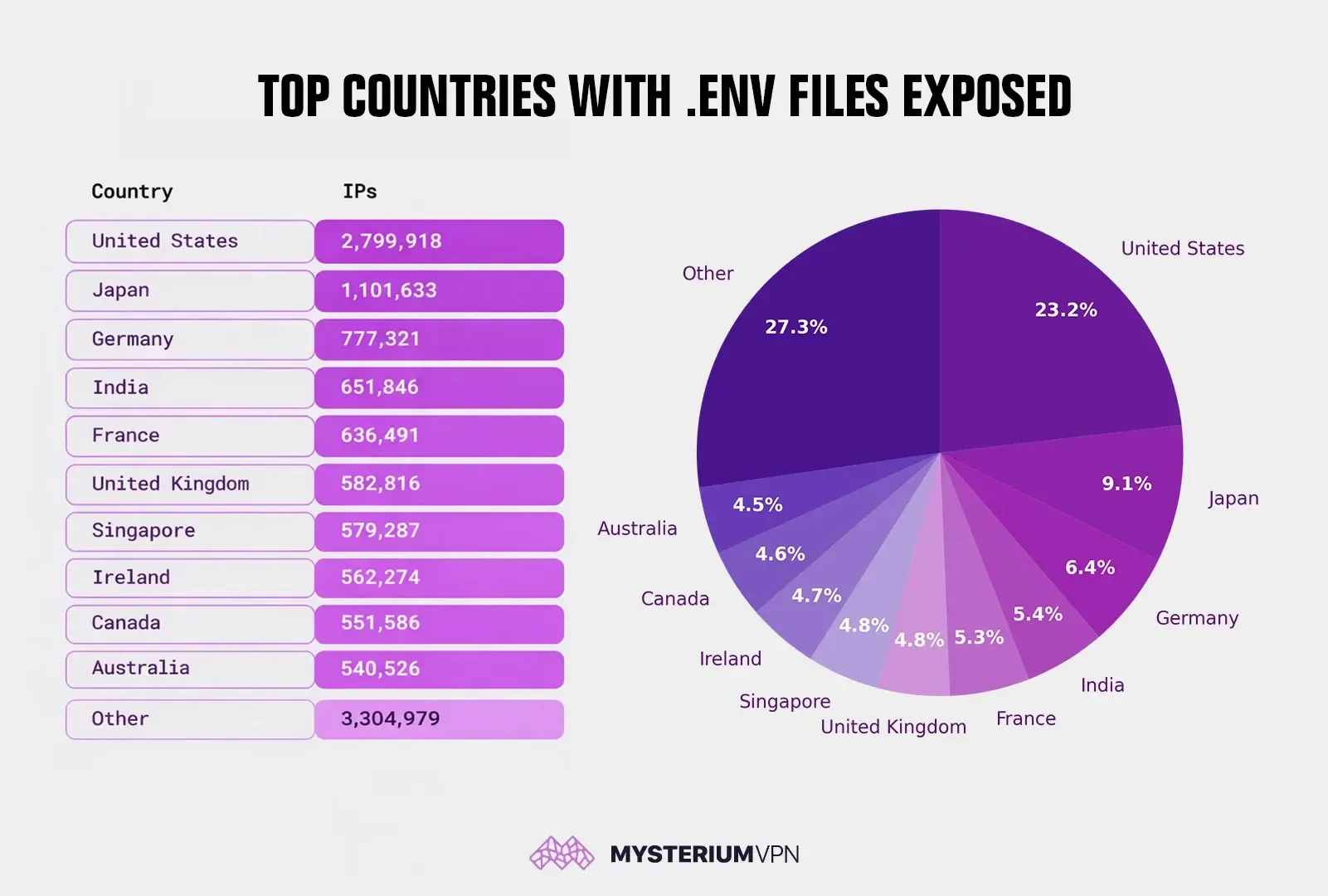
The United States leads the count, with nearly 2.8 million exposed IPs, followed closely by Japan, Germany, India, France, and the UK. The global exposure of .env files paints a disturbing picture of widespread security misconfigurations that can have devastating consequences for organizations. Database credentials enable data theft and privilege escalation, API keys invite financial abuse and spam campaigns, leaked JWT secrets allow attackers to forge tokens and hijack accounts, SMTP credentials open the door to phishing from legitimate domains, and cloud storage keys expose backups, identity documents, and internal files.
So, what are the common causes of this widespread security failure? In many cases, it comes down to human error, such as missing deny rules for hidden files, reverse proxies forwarding sensitive paths, static roots pointing to entire project directories, container images embedding secrets, or forgotten backup files like .env.bak or .env.old. Attackers regularly scan for these predictable patterns, making it easier for them to exploit.
When teams discover an exposed .env file, they must treat the event as a full security incident, removing public access immediately, purging caches, and rotating every secret in the file. It's essential to implement automated secret scanning in repositories and CI pipelines to prevent similar incidents in the future.
To mitigate this risk, organizations need to adopt a more proactive approach to secret management. This involves blockading hidden and backup files at the server and CDN level, moving secrets out of web-accessible directories and into centralized secret management systems with audit logs and automated rotation. Scope keys to minimal permissions, enforce network restrictions, and adopt short-lived tokens.
The Mysterium VPN findings highlight a systemic issue: secret exposure continues at massive scale because teams treat configuration as an afterthought. Security teams must embed secret governance into development workflows, deployment pipelines, and infrastructure baselines to prevent such breaches from happening in the first place.
In conclusion, the widespread exposure of .env files is a wake-up call for organizations to revisit their security posture and take proactive measures to protect sensitive information. By adopting robust secret management practices, developers can help prevent similar incidents and ensure that organizations are better equipped to handle future threats.
Stay ahead of the threat curve by staying informed about the latest cybersecurity developments. Follow me on Twitter: @securityaffairs and Facebook and Mastodon for the latest news and insights into the world of hacking and cybersecurity.