UAT-10027 Campaign Hits U.S. Education and Healthcare with Stealthy Dohdoor Backdoor
The cybersecurity landscape has witnessed numerous threats in recent times, but a recent campaign that has garnered significant attention is the UAT-10027 threat cluster targeting U.S. education and healthcare sectors. Researchers at Cisco Talos have identified this new campaign as a stealthy deployment of a previously unseen backdoor named Dohdoor.
This threat cluster initially gained traction since December 2025, with initial access likely occurring through phishing attacks that triggered a PowerShell script to download a malicious batch file and then a disguised DLL via sideloading. The malware utilizes DNS-over-HTTPS and Cloudflare infrastructure to hide its command-and-control (C2) traffic within legitimate HTTPS connections. This allows attackers to deploy additional payloads, such as Cobalt Strike, directly into memory while evading security detection and maintaining persistent access.
The attack vector begins with phishing emails that trick victims into running a PowerShell script. The script downloads a batch file, which in turn downloads a disguised malicious DLL via sideloading. The malware then uses DNS-over-HTTPS to query Cloudflare over port 443, builds crafted HTTP requests, and parses JSON responses to obtain the C2 IP address.
The Dohdoor backdoor is deployed as a 64-bit DLL loader compiled in November 2025. This loader resolves Windows APIs through hash-based lookups, parses command-line arguments from sideloaded executables, and extracts the C2 URL and payload path. The malware uses DNS-over-HTTPS to query Cloudflare over port 443 to retrieve an encrypted payload.
Upon decryption using a custom XOR-SUB algorithm with SIMD routines for 16-byte blocks and a position-dependent formula for remaining bytes, Dohdoor sends HTTPS GET requests that mimic curl traffic to retrieve the encrypted payload. This process involves decrypting data maintained at a 4:1 expansion ratio where the decrypted data is four times smaller than the encrypted data.
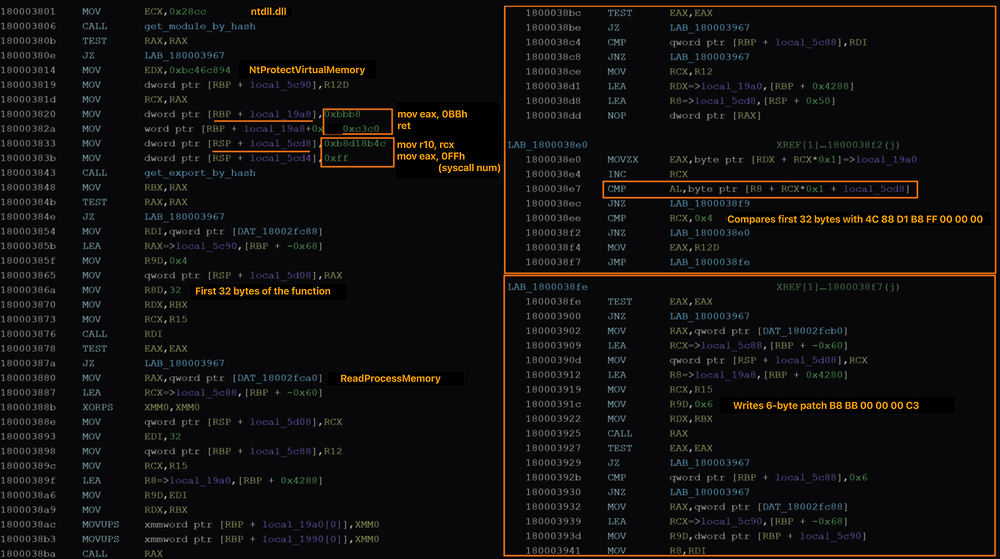
The loader then performs process hollowing by injecting the decrypted payload into suspended Windows binaries like OpenWith.exe or wksprt.exe before resuming execution. To evade Enhanced Detection (EDR), Dohdoor locates ntdll.dll, checks NtProtectVirtualMemory for user-mode hooks, and patches the syscall stub to create a direct syscall trampoline.
Talos assesses with low confidence that UAT-10027 links to North Korea due to overlaps with the Lazarus Group. Dohdoor shares traits with Lazarloader, including a custom XOR-SUB routine using the 0x26 constant and NTDLL unhooking for EDR evasion. The campaign also utilizes DoH via Cloudflare, DLL sideloading, process hollowing, and mixed-case TLDs—tradecraft seen in Lazarus operations.
While UAT-10027's malware shares technical overlaps with the Lazarus Group, the campaign's focus on education and healthcare sectors deviates from Lazarus' typical profile of cryptocurrency and defense targeting. Notably, North Korean APT actors have targeted the healthcare sector using Maui ransomware, and another group, Kimsuky, has targeted the education sector.
In conclusion, UAT-10027 represents a significant threat to U.S. education and healthcare sectors. Its use of advanced techniques such as DNS-over-HTTPS, Cloudflare infrastructure, and custom XOR-SUB algorithms for decryption highlights the evolving nature of cyber threats. It is essential for organizations in these sectors to remain vigilant and implement robust security measures to prevent similar attacks.
---
Note: The original content has been rewritten while preserving key facts and details.