# AI-Driven Cybercrime: The Brief but Lethal Campaign of Arkanix Stealer
In the ever-evolving landscape of cybersecurity, it's not uncommon to come across malware that is as fascinating as it is threatening. The recent emergence of Arkanix Stealer, a sophisticated information-stealing malware, has left researchers and security experts alike scratching their heads. This brief yet lethal campaign, which surfaced in late 2025, was likely the result of an AI-assisted experiment gone wrong.
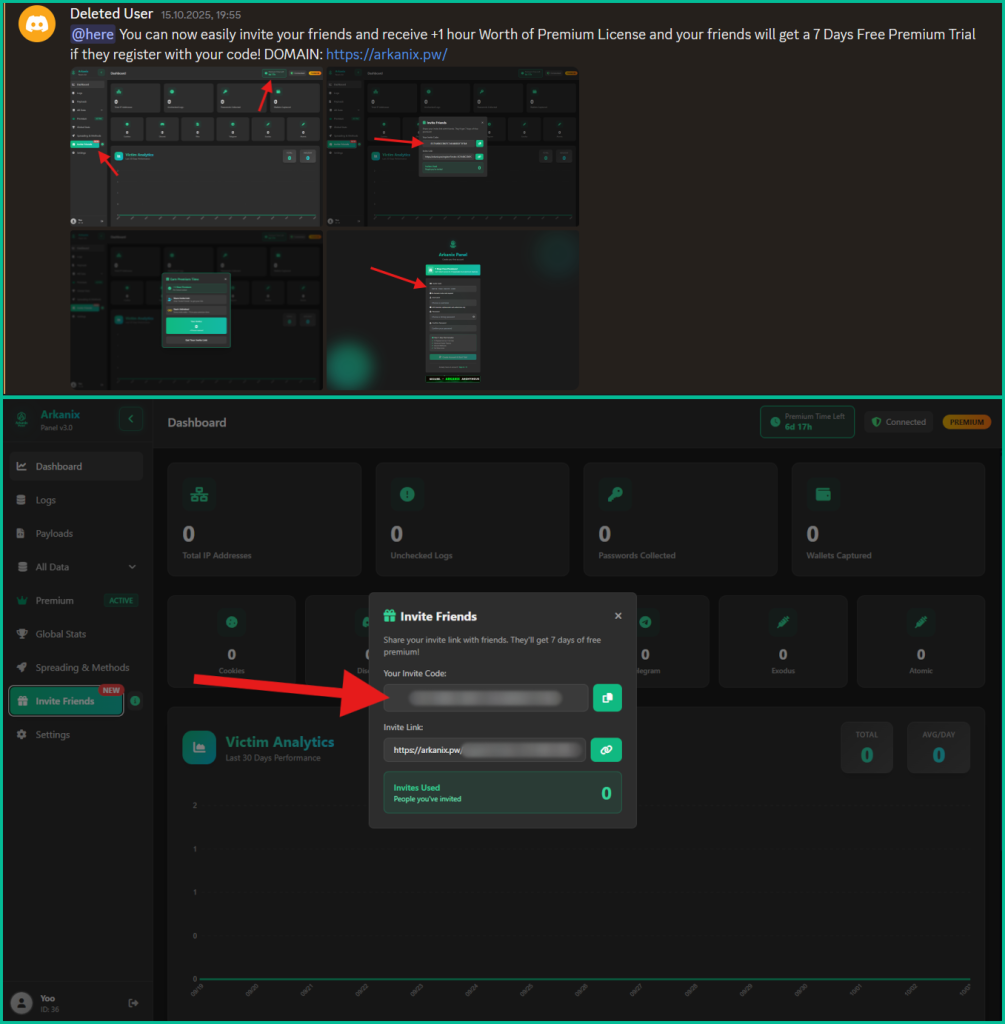
Arkanix Stealer emerged on dark web forums as a short-lived MaaS (Machine-as-a-Service) offering with a control panel and configurable payloads. It used a C++ build embedding ChromElevator to steal system and crypto wallet data, along with a packed Python version with dynamic configuration. The operation was likely spread via phishing-themed lures, with the initial infection vector remaining unclear. However, phishing-themed loaders suggest social-engineering attacks as the primary means of exploitation.
The malware's control panel allowed operators to configure payloads, including an additional dropper that deployed before data theft. Arkanix Stealer collected extensive system details, browser data (passwords, cookies, crypto-related info), Telegram sessions, Discord credentials, VPN data, and selected user files, packing the results into archives for exfiltration. What's particularly noteworthy about this malware is its ability to extract various types of data from supported browsers, including Google Chrome and the Tor Browser.
The list of supported browsers is hardcoded, and unlike other parameters, it cannot be modified during execution. The stealer itself supports the extraction of diverse information, such as:
* Extra modules, including wallet tools and HVNC * Dynamic feature updates from the panel
After completing operations, Arkanix Stealer deletes itself and related artifacts. Researchers analyzed both debug and release builds of the native C++ Arkanix Stealer, revealing that the release version used VMProtect and the arkanix[.]pw C2, while the debug build relied on a Discord bot and extensive logs.
The malware also embeds the ChromElevator browser extractor for credential theft and encrypts exfiltrated data with AES-GCM + PBKDF2. The infrastructure observed by experts included two domains behind Cloudflare hosting a protected panel that was taken offline later. The group promoted the stealer via Discord with marketing tactics, a referral program, and promises of a crypter, suggesting a short-lived, possibly AI-assisted development.
Key indicators of compromise (IoCs) for Arkanix Stealer include:
* A link to a Discord server used as the primary communication channel * Phishing-themed lures used to spread the malware * The use of LLMs (Large Language Models) in its development
While being quite functional, Arkanix Stealer contains probable traces of LLM-assisted development, which suggests that such assistance might have drastically reduced development time and costs. This campaign tends to be more of a one-shot campaign for quick financial gains rather than a long-running infection.
In conclusion, the brief but lethal campaign of Arkanix Stealer serves as a stark reminder of the evolving nature of cybercrime and the importance of staying vigilant in the face of emerging threats. As security experts continue to monitor the landscape, it's essential to remain aware of the latest trends and tactics employed by malicious actors.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon for the latest updates on cybersecurity news and research.