**Privacy Risks in Next Generation Smart Home Systems**
Living with Smart Homes: The Unseen Risks of Convenience
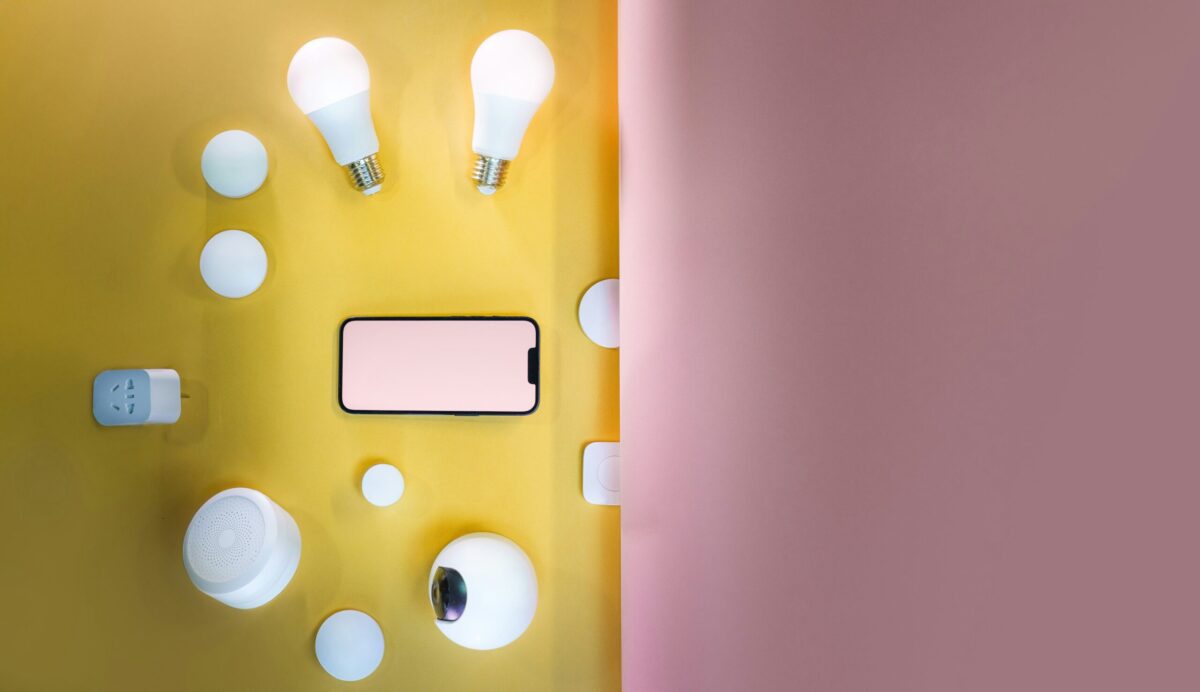
The idea of a fully connected home was once the realm of science fiction, but today it's an everyday reality. Smart devices promise convenience, efficiency, and comfort, but they also come with a shadow: privacy risks. These devices gather massive amounts of personal data, raising questions about how that data is handled, stored, or exploited.
The Layering of Sensors, Cloud Connectivity, and Data Collection
Smart thermostats learn your schedule, voice assistants respond to natural language, and connected security cameras monitor your front door. These devices seem like small conveniences, but they transform your home into a complex digital environment. The level of surveillance these systems enable is unprecedented, and often not transparent.
We assume our private space remains private, but that assumption may be misplaced in a world where devices are always listening, watching, and communicating. Understanding the risks involves more than listing potential vulnerabilities; it's about grappling with what it means to bring the internet inside our walls and weigh the tradeoffs between convenience and control.
The Concern Goes Beyond Targeted Ads or Data Breaches
It's not just about targeted advertising or data breaches. The concern is about the fundamental shift in how personal information circulates in everyday life and who truly owns it. Familiarity with technology doesn't guarantee security; most users encounter smart home devices through flashy demos or simple setup guides that rarely delve into privacy implications.
Business Models Play a Big Role in Data Collection
Many companies monetize user data directly or indirectly through advertising partnerships and service enhancements, incentivizing broad data gathering over privacy. The irony is that smart home products are sold as convenience tools but become data collection gateways for corporate interests.
The Complexity of Device Ecosystems
Smart home devices collect data through sensors, which can be innocuous alone but paints a detailed picture when combined over time. The frequency of firmware updates and cloud syncs creates multiple points where privacy can fray. A core challenge lies in device ecosystems, as many users mix products from different brands with varying privacy policies and security standards.
Passive Tracking: A Silent Threat to Privacy
Sensors like smart lights or thermostats can indirectly reveal occupancy patterns without explicit permission. Behavioral profiling is increasingly common, analyzing when lights turn on and off, doors open or close, and even voice tone or volume to guess household occupants' habits and preferences.
Real World Implications of Privacy Breaches
There have been incidents where hackers remotely accessed cameras or microphones, exposing families to invasions of privacy. Data collected through smart home devices has reportedly been used in legal disputes or insurance claims, underscoring how this data can impact lives in unexpected ways.
A Conversation Worth Having: Privacy and Ownership
The conversation about privacy often gets put aside when new smart devices appear. The focus tends to be on features and ease of use rather than raising questions about data rights and user control. We know from everyday life that people expect their homes to be sanctuaries, but the introduction of devices potentially recording conversations or tracking movements feels at odds with common sense.
Frequently Asked Questions About Privacy in Smart Homes
- What are the biggest privacy risks in smart home systems? Major risks include unauthorized access to devices, persistent data collection by manufacturers, cloud data breaches, and passive tracking through sensors that reveal personal habits and household occupancy.
- Can smart home devices be used to spy on users? Yes, smart devices with microphones or cameras can be exploited to spy. Although manufacturers build protections, vulnerabilities or intentional data retention policies may expose users to audio or video surveillance without explicit consent.
- How can I limit data sharing from my smart home devices? Users can reduce data sharing by adjusting privacy settings, disabling features like voice recordings retention when possible, regularly updating device firmware, and choosing products that process data locally rather than relying on cloud services.
A Thoughtful Pause on Privacy's Place
Living with smart home technology often means accepting some level of tradeoff between ease and privacy. Having watched many friends and family members juggle these devices, I notice people seldom stop to consider what they really sacrifice. Is it worth the slight gain in convenience to give away daily routines and personal details? Privacy in our homes feels abstract until something goes wrong or until users see ads eerily aligned with private conversations.
Despite all the hype around smart living, one lesson stands out: not all conveniences come free, and privacy is one currency no one can replenish once spent unwisely. It might sound clichéd to suggest cautious adoption, but that's what experience shows. Choose devices thoughtfully, read terms, check security updates, and pay attention to how your data moves around.