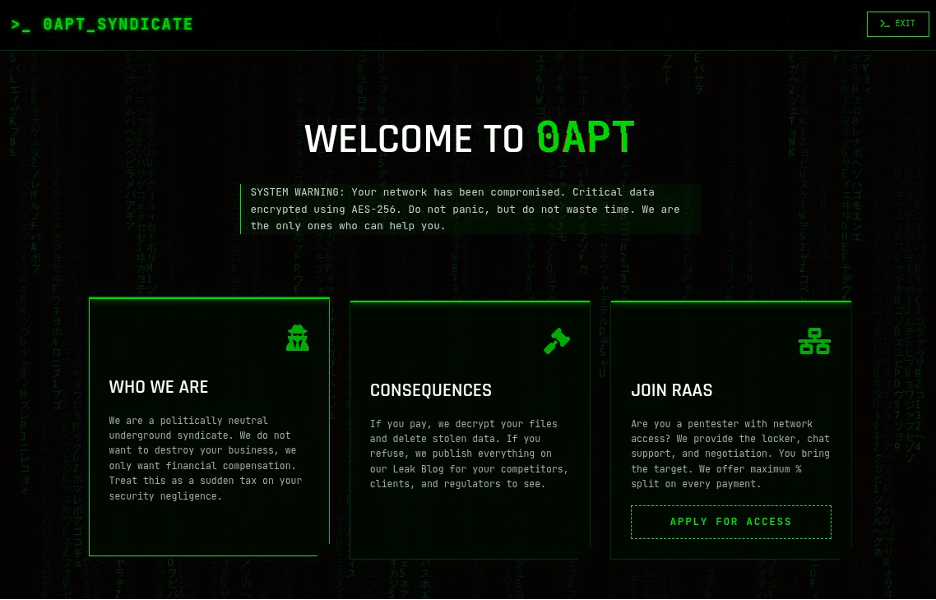
**New Cybercrime Group 0APT Accused of Faking Hundreds of Breach Claims**
A recent investigation has uncovered a sophisticated cybercrime group, known as 0APT, which is accused of faking hundreds of breach claims. The group's modus operandi involves infiltrating key US infrastructure through seemingly innocuous means – GIFs and SVGs.
**The AsyncRAT Malware: A Silent Threat**
At the heart of 0APT's operation is a piece of malware known as AsyncRAT, a remote-access tool (RAT) that allows attackers to remotely control compromised systems. This versatile malware can spread through various means, including phishing emails, exploit kits, and – in this case – unsuspecting GIFs and SVGs.
AsyncRAT's ability to evade detection makes it a formidable threat. It uses advanced techniques such as code obfuscation and encryption to remain hidden from security software. Once installed on a system, the malware can harvest sensitive information, including login credentials, financial data, and more.
**The GIF and SVG Gambit**
0APT's tactics are particularly cunning, leveraging the trust inherent in image files to infiltrate key US infrastructure. The group creates malicious GIFs or SVGs that contain embedded code for AsyncRAT. These seemingly harmless images are often used as attachments in phishing emails or shared on social media platforms.
When a user opens the malicious file, their system is compromised, and AsyncRAT is installed without their knowledge. This allows 0APT to gain unauthorized access to sensitive areas of targeted networks, including financial institutions, government agencies, and critical infrastructure providers.
**Faking Breach Claims: A New Low**
But that's not all – 0APT takes its deception further by fabricating breach claims to cover their tracks. The group creates fake reports, attributing the intrusion to a previously unknown vulnerability or a sophisticated nation-state actor. This tactic has allowed them to exploit vulnerabilities in existing incident response plans and gain leverage for future attacks.
As the investigation continues, it becomes clear that 0APT's operation is more extensive than initially thought. Hundreds of breach claims have been attributed to the group, with many more likely to be discovered. The scale of their deception raises questions about the effectiveness of current security measures and highlights the need for enhanced threat intelligence and incident response strategies.
**Conclusion**
The 0APT cybercrime group's use of AsyncRAT malware and malicious GIFs/ SVGs poses a significant threat to key US infrastructure. Their ability to fake breach claims has compromised trust in existing security protocols, making it imperative that organizations reassess their defenses and invest in advanced threat detection tools.
As the cybersecurity landscape continues to evolve, one thing is clear: 0APT's tactics will only continue to adapt and improve unless a concerted effort is made to disrupt their operation. The question remains – will we be able to stay ahead of these sophisticated attackers, or will they succeed in exploiting our vulnerabilities?
**Related Stories**
* [Investigation Uncovers Sophisticated Cybercrime Group Targeting Financial Institutions](link) * [AsyncRAT Malware: A Comprehensive Guide to the Silent Threat](link)