**Nearly 5 Million Web Servers Found Exposing Git Metadata – Study Reveals Widespread Risk of Code and Credential Leaks**
A new study by the Mysterium VPN research team has uncovered a staggering issue affecting millions of web servers worldwide. The study reveals that nearly 5 million public web servers are exposing Git repository metadata, leaving them vulnerable to attacks that can lead to code theft, credential abuse, and even supply-chain attacks.
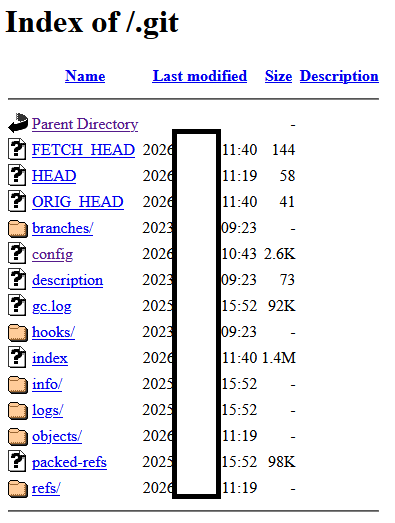
The research team discovered that over 4.96 million IPs have publicly accessible `.git` directories, while a whopping 252,733 `.git/config` files contained active deployment credentials – approximately 5% of the total number of exposed files. This means that an attacker could potentially reconstruct source code, steal secrets, and gain direct access to sensitive information.
The study highlights the severity of this issue by listing the top affected regions: the United States, Germany, and France. Exposed metadata can have far-reaching consequences, including:
- Credential theft
- Malicious commits
- Cloud access
The issue persists due to various reasons such as deployment mistakes, hidden folders going live, and servers not blocking them by default. This turns small errors into serious breaches.
The research team notes that even a 5% credential exposure rate translates to hundreds of thousands of usable secrets. To prevent this, teams should implement server rules, secrets management, pre-commit checks, monitoring, and rapid response plans.
"The findings highlight a widespread issue caused by deployment practices, inconsistent server configuration, and misplaced assumptions about safety," concludes the report. "While the presence of exposed Git metadata alone is dangerous, the inclusion of credentials dramatically increases risk, enabling repository takeover, supply chain attacks, and access to cloud infrastructure."
The research team emphasizes that even small percentages of credential exposure can become severe at an internet scale, making it easy for attackers to automate discovery.
Read the full write-up on the Mysterium VPN blog: https://www.mysteriumvpn.com/blog/news/git-metadata-leak
**About the Study**
* 4.96M IPs found with publicly accessible `.git` directories * 252,733 `.git/config` files contained active deployment credentials (~5%) * Top affected regions: United States, Germany, and France * Exposed metadata can lead to credential theft, malicious commits, and cloud access
**What You Can Do**
* Implement server rules and secrets management * Use pre-commit checks and monitoring * Develop rapid response plans * Block public access to `.git` folders * Rotate any leaked credentials