**Record-Breaking 31.4 Tbps DDoS Attack Hits in November 2025, Stopped by Cloudflare**
A massive Distributed Denial of Service (DDoS) attack, peaking at a record-breaking 31.4 Terabits per second (Tbps), was launched against Cloudflare customers in November 2025. The attack, which lasted just 35 seconds, was automatically detected and blocked by the security firm.
The AISURU/Kimwolf botnet, linked to the record-breaking DDoS attack, was found to be operating as a DDoS-for-hire service, targeting broadband providers with attacks exceeding 1.5Tb/sec from infected customer devices. The botnet, which has been linked to over 1.8 million devices and issued more than 1.7 billion DDoS attack commands, uses UDP, TCP, and GRE floods with medium-sized packets and randomized ports/flags.
**A Surge in Hyper-Volumetric HTTP DDoS Attacks**
According to Cloudflare's report, the November 2025 incident was part of a surge in hyper-volumetric HTTP DDoS attacks observed in late 2025. The firm noted that throughout 2025, there was a continuous increase in these types of attacks, with a 40% increase in Q4 compared to the previous quarter.
**The Rise of Hyper-Volumetric Attacks**
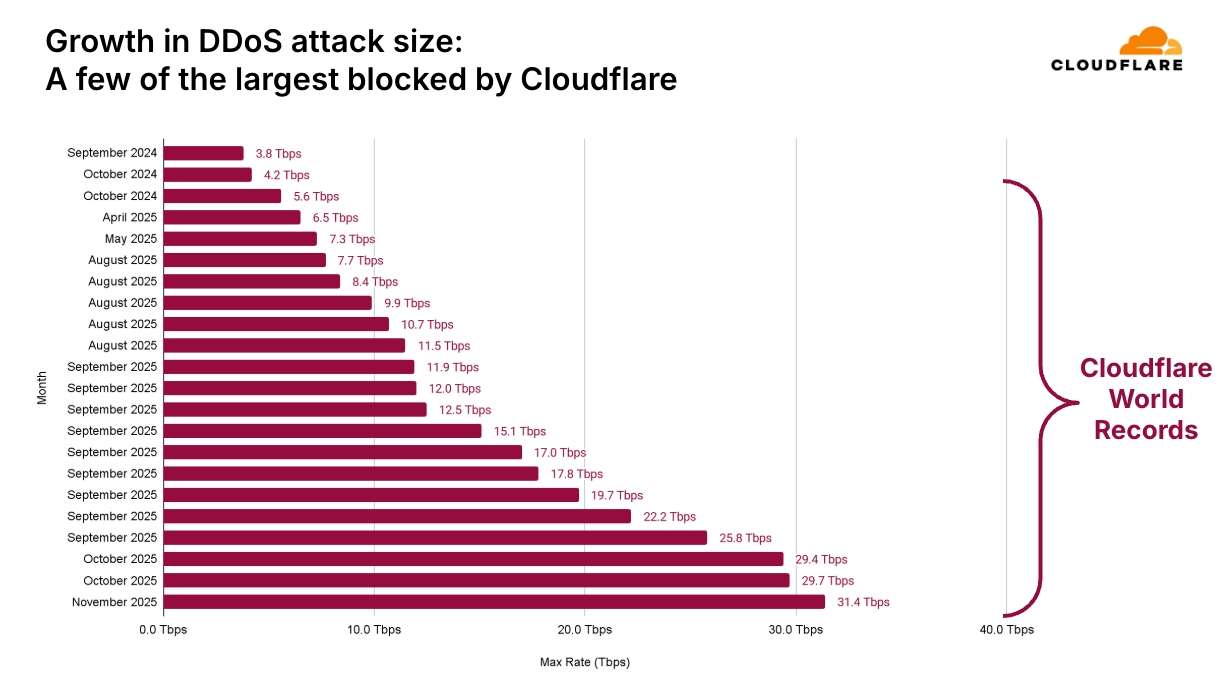
Cloudflare's report highlighted the rapid growth in DDoS attack sizes, with one attack reaching 31.4 Tbps in a DDoS attack that lasted just 35 seconds. The graph below illustrates the significant increase in DDoS attack sizes over the course of 2025.

**The Kimwolf Android Botnet**
A newly discovered Android botnet, linked to the Aisuru botnet, has been found to have infected over 1.8 million devices and issued more than 1.7 billion DDoS attack commands. The Kimwolf botnet primarily targets TV boxes and uses a range of malicious functions, including DDoS, proxy forwarding, reverse shell, and file management.
**Global Targets**
The largest DDoS attacks in Q4 2025 mainly targeted Cloudflare customers in the Telecommunications, Service Providers, and Carriers sector, followed by Gaming and Generative AI services. Cloudflare's own infrastructure was also attacked using HTTP floods, DNS attacks, and UDP floods.
**Regional Breakdown**
Globally, China, the United States, Germany, and Brazil remained among the most targeted countries, while Hong Kong and especially the United Kingdom saw sharp increases in attacks. Regarding attack origins, Bangladesh became the top source of DDoS traffic, overtaking Indonesia, with notable rises also seen from Ecuador and Argentina.
**Attack Origins**
Most DDoS attacks in Q4 2025 originated from IPs linked to major cloud platforms like DigitalOcean, Microsoft, Tencent, Oracle, and Hetzner, mostly in the U.S. Telcos in Asia-Pacific also contributed. Attacks are global, using thousands of source networks.
**Cloudflare's Defense Strategy**
Cloudflare offers a free DDoS Botnet Threat Feed, with 800+ networks collaborating to identify and shut down abusive IPs. "DDoS attacks are rapidly growing in sophistication and size, surpassing what was previously imaginable," concludes the report. "This evolving threat landscape presents a significant challenge for many organizations to keep pace."