**China-linked Amaranth-Dragon Hackers Target Southeast Asian Governments in 2025**
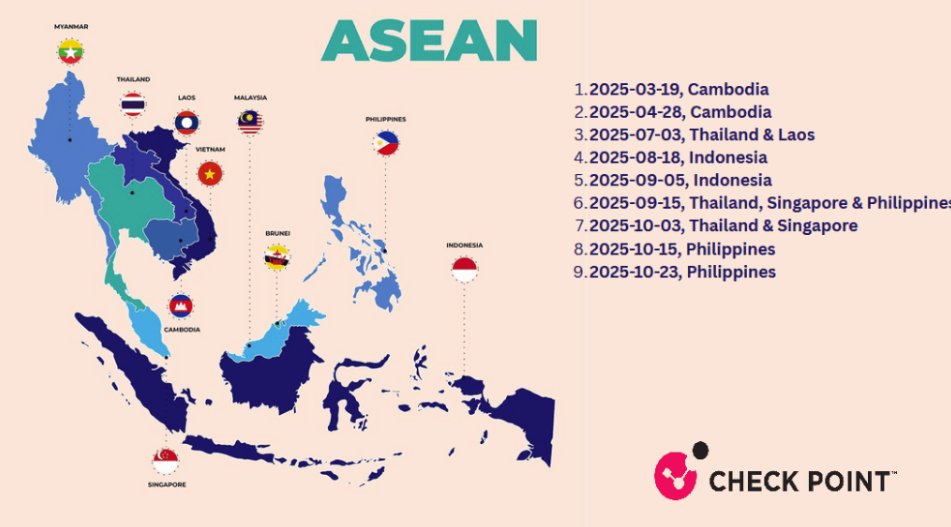
In a disturbing trend, China-linked hackers tracked as Amaranth-Dragon have been targeting government and law enforcement agencies across Southeast Asia since 2025. According to CheckPoint Research, these sophisticated threat actors carried out cyber-espionage campaigns against high-profile targets in Thailand, Indonesia, Singapore, and the Philippines.
CheckPoint's investigation has revealed a strong connection between Amaranth-Dragon and APT41, one of China's most notorious hacking groups. The attacks are characterized by their stealthy nature and long-term espionage goals, rather than disruption or financial gain. This level of sophistication suggests that Amaranth-Dragon is part of the larger APT41 ecosystem.
The attacks began on August 18, 2025, just days after a publicly disclosed flaw in WinRAR software (CVE-2025-8088) was exploited by hackers. The vulnerability, which allows arbitrary code execution, was first disclosed on August 8, 2025, and a public exploit was released on August 14.
Victims were likely lured into opening malicious archives hosted in the cloud via spear-phishing emails. Upon opening these files, a loader using DLL side-loading would be triggered, which would decrypt and run the Havoc C2 framework entirely in memory. This tactic is linked to APT41 and allows for sophisticated remote access capabilities.
Earlier campaigns by Amaranth-Dragon used ZIP files with LNK and BAT scripts, while later ones targeted Indonesia with password-protected RARs delivering a TGAmaranth RAT controlled via a Telegram bot. The RAT supports process listing, screenshots, command execution, and file transfer, giving the attackers unparalleled access to compromised systems.
The C2 setup is carefully hidden behind Cloudflare and restricted to specific countries, demonstrating Amaranth-Dragon's attention to detail and operational discipline. CheckPoint Research has found strong links between Amaranth-Dragon and APT41, including similar tools, coding patterns, and UTC+8 operations.
"The campaigns by Amaranth-Dragon exploiting the CVE-2025-8088 vulnerability highlight the recent trend of sophisticated threat actors rapidly weaponizing newly disclosed vulnerabilities," says CheckPoint Research. "By leveraging a path traversal flaw in WinRAR, the group demonstrates its ability to adapt its tactics and infrastructure to maximize impact against highly targeted government and law enforcement organizations across Southeast Asian countries."
The report concludes by emphasizing the importance of timely vulnerability management, user awareness, and robust defense-in-depth strategies in the face of such sophisticated threats.
**Key Takeaways:**
* China-linked hackers tracked as Amaranth-Dragon have been targeting government and law enforcement agencies across Southeast Asia since 2025. * Strong links have been found between Amaranth-Dragon and APT41, including similar tools, coding patterns, and UTC+8 operations. * The attacks are characterized by their stealthy nature and long-term espionage goals, rather than disruption or financial gain. * Victims were likely lured into opening malicious archives hosted in the cloud via spear-phishing emails. * Amaranth-Dragon has demonstrated its ability to adapt its tactics and infrastructure to maximize impact against highly targeted organizations.
**Follow us on social media:**
* Twitter: @securityaffairs * Facebook: @securityaffairs * Mastodon: @securityaffairs