**Notepad++ Infrastructure Hack Likely Tied to China-Nexus APT Lotus Blossom**
The Notepad++ hosting breach, which was revealed in recent weeks, has been linked to a sophisticated attack attributed to the China-nexus APT group known as Lotus Blossom. According to Rapid7 researchers, the attackers compromised the hosting provider's infrastructure, redirecting update traffic to malicious servers.
The incident began in June 2025 and is believed to have lasted until December 2, 2025. The attackers exploited vulnerabilities in the hosting provider's system to gain access to Notepad++ update traffic, which was then redirected to attacker-controlled servers. The exact technical mechanism of the attack remains under investigation, but it is clear that the compromise occurred at the hosting provider level rather than through any flaws in Notepad++ code.
Multiple researchers have linked the attack to a Chinese state-sponsored group based on its highly selective targeting. The attackers compromised a shared hosting server until September 2, 2025, and later used stolen internal credentials to redirect Notepad++ update traffic to malicious servers until December 2. After completing these actions, the provider reviewed system logs and confirmed there was no evidence of continued attacker access or malicious activity.
However, a detailed investigation by Rapid7 Labs and its MDR team uncovered a sophisticated campaign tied to the China-linked APT Lotus Blossom. The group has been active since 2009 and is known for running targeted espionage against government, telecom, aviation, critical infrastructure, and media organizations, mainly in Southeast Asia and Central America.
The researchers discovered that the attackers used a custom backdoor, dubbed Chrysalis, along with stealthy loaders that abuse Microsoft Warbird to conceal malicious code execution. "Our investigation identified a security incident stemming from a sophisticated compromise of the infrastructure hosting Notepad++, which was subsequently used to deliver a previously undocumented custom backdoor, which we have dubbed Chrysalis," reads the report published by Rapid7.
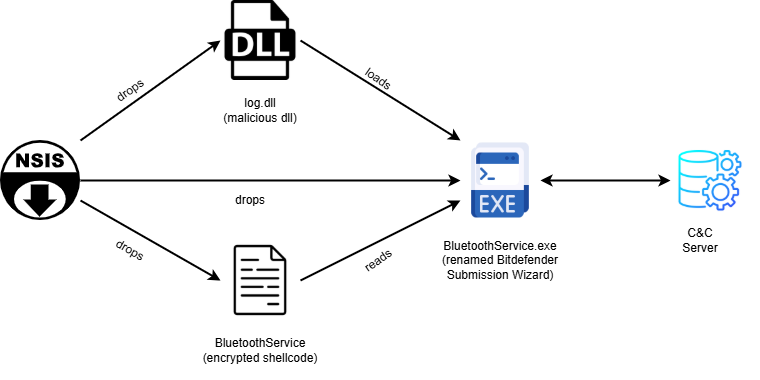
Rapid7's MDR team traced the initial access to abuse of Notepad++ distribution infrastructure. Investigators saw notepad++.exe and GUP.exe run first, followed by a suspicious update.exe downloaded from an external IP. That file turned out to be an NSIS installer, a delivery method often used by Chinese APT groups.
The malware relied on multiple layers of obfuscation to conceal its code and make analysis harder. It used custom API hashing to avoid calling Windows functions directly and encrypted its configuration to hide key settings. After running, it set up persistence to survive reboots, collected detailed information about the infected system, and connected to a remote command-and-control server.
Through this connection, attackers could run commands, move files, and take full control of compromised machines. Chrysalis supports full remote control, including command execution, file transfer, and interactive shells. Investigators also uncovered related loaders abusing Metasploit shellcode, Cobalt Strike beacons, and even Microsoft Warbird protections, showing long-term development and a complex, multi-stage attack chain.
The researchers attribute the campaign to Lotus Blossom based on strong overlaps with prior Symantec research, including a renamed Bitdefender tool used to sideload log.dll, similar loader chains, and shared Cobalt Strike public keys across multiple samples. "The discovery of the Chrysalis backdoor and the Warbird loader highlights an evolution in Billbug's capabilities," concludes the report.
"What stands out is the mix of tools: the deployment of custom malware (Chrysalis) alongside commodity frameworks like Metasploit and Cobalt Strike, together with the rapid adaptation of public research (specifically the abuse of Microsoft Warbird)."