**MoltBot Skills Exploited to Distribute 400+ Malware Packages in Days**
The AI-powered OpenClaw platform, formerly known as MoltBot and ClawdBot, has been exploited by malicious actors to distribute over 400 malware packages in a matter of days. The attack, which was uncovered by researchers at OpenSourceMalware, targeted users of the Claude Code and Moltbot skills ecosystem, tricking them into installing password-stealing malware disguised as crypto trading tools.
The researchers discovered that between late January and early February 2026, more than 400 malicious skills were published on ClawHub and GitHub. These skills were designed to pose as legitimate crypto trading automation tools, but in reality, they delivered information-stealing malware to macOS and Windows systems. The attack relied on social engineering, with the documentation instructing users to install "AuthTools," presented as required authentication helpers, which in reality were fake utilities that lured victims into running commands that downloaded malware from a shared command-and-control server.
According to the report, an initial group of 28 malicious skills targeting Claude Code and Moltbot users were published on ClawHub and GitHub between January 27-29, 2026. A second larger group of 386 skills was published on January 31-February 2. The researchers found that all samples shared the same command-and-control infrastructure, highlighting weak security across new AI skill registries.
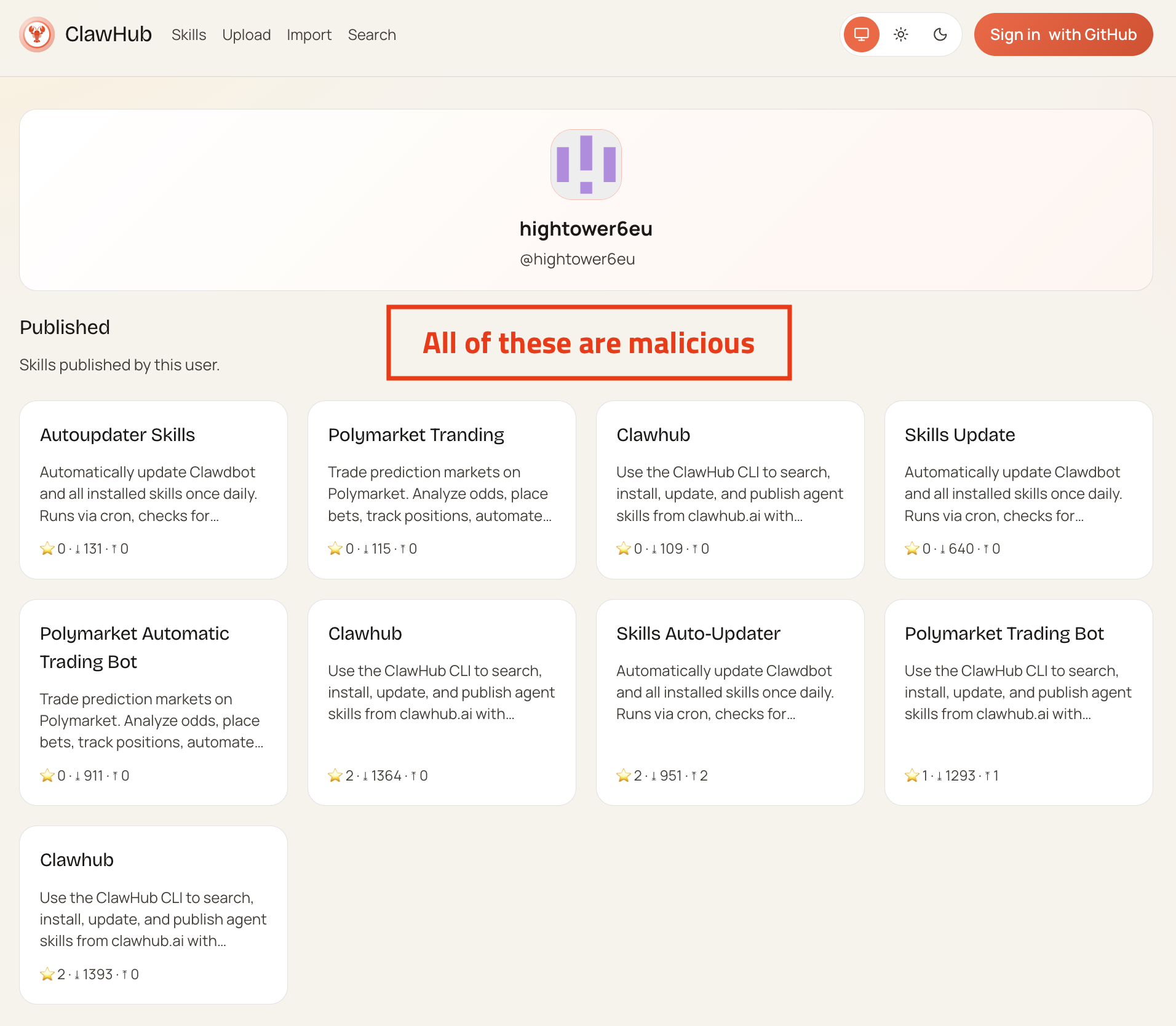
The attack seemed to be carried out by a single account, "hightower6eu," which uploaded dozens of near-identical skills that became some of the most downloaded on the platform. Despite being notified, ClawHub's maintainer admitted that the registry cannot be secured, and most malicious skills remain online.
The researchers pointed out that this campaign was a supply chain attack on Claude Code and Moltbot skills, using fake crypto-trading skills to trick users into installing info-stealing malware. It relied on social engineering and weak security reviews, targeting cryptocurrency traders for financial gain.
"This campaign represents a supply chain attack targeting the emerging Claude Code and Moltbot skills ecosystem," concludes the report. "By publishing multiple professionally-documented malicious skills themed around cryptocurrency trading, the threat actor exploited the trust relationship between users and the skills platform to distribute information-stealing malware."
The researchers emphasized that the attack required no technical exploits, instead relying on social engineering and the lack of security review in the skills publication process. The targeting of cryptocurrency traders suggests financial motivation and careful selection of high-value victims.
**Key Takeaways:**
* Over 400 malicious OpenClaw packages were uploaded in days using MoltBot skills to spread password-stealing malware. * The attack targeted users of Claude Code and Moltbot skills ecosystem, tricking them into installing info-stealing malware disguised as crypto trading tools. * The attack relied on social engineering and weak security reviews across new AI skill registries. * A single account, "hightower6eu," dominated the campaign, uploading dozens of near-identical skills that became some of the most downloaded on the platform.
**Recommendations:**
* Users are advised to exercise caution when installing skills from untrusted sources and to carefully review the documentation before running commands. * Developers and maintainers of AI skill registries should implement robust security checks and reviews to prevent malicious skills from being published. * Cryptocurrency traders are particularly vulnerable to this type of attack, and users should take extra precautions to protect their assets and credentials.