**Cyberattacks Disrupt Communications at Wind, Solar, and Heat Facilities in Poland**
On December 29, 2025, Poland faced a coordinated cyberattack targeting over 30 wind and solar farms, a manufacturing company, and a major heat and power plant serving nearly 500,000 people. The attacks were attributed to a threat cluster called Static Tundra, linked to Russia's FSB Center 16, although other firms suggest involvement from the Russian-linked APT Sandworm.
The cyberattacks aimed to cause disruption during a period of severe winter weather, but the attackers only impacted communications. Electricity generation and heat supply were not interrupted, thanks to the resilience of the facilities' systems. The attacks marked a rare and serious escalation, impacting both IT systems and physical industrial equipment (OT).
CERT Polska published a report to raise awareness of the growing risk of cyber sabotage in the energy sector. According to the report, analysis of the infrastructure used in the attack showed a high degree of overlap with the infrastructure used by Static Tundra, including compromised VPS servers, routers, traffic patterns, and characteristics of anonymizing infrastructure.
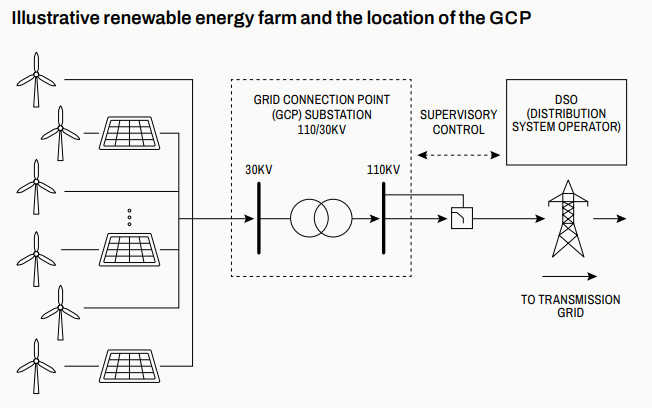
The attackers targeted power substations that connect wind and solar plants to the grid. They focused on industrial devices like controllers, HMIs, protection relays, and network equipment. In one instance, they infiltrated a CHP plant's internal network and spent months stealing sensitive information and gaining privileged access. When they tried to activate malware designed to destroy data, the plant's EDR system stopped the attack.
The attackers used previously unknown wiper malware, called DynoWiper, which corrupted and deleted files across disks by overwriting parts of them with random data, making recovery impossible. They also used a PowerShell script named LazyWiper, which targeted a wide range of file types and partially overwrote files to render them unusable.
Investigators identified two tools used in the attacks: DynoWiper and LazyWiper. The researchers noted that DynoWiper had no command-and-control, no persistence, and made no effort to hide. LazyWiper targeted a wide range of file types and partially overwrote files to render them unusable; analysts believe part of it may have been generated using an AI tool.
The attackers spread the malware through Active Directory using malicious Group Policy tasks to run it across networks. CERT Polska found that the attackers used compromised VPS servers and Cisco routers, with infrastructure matching patterns linked to Static Tundra. The overlap was not strong enough for firm attribution, but recent reports from ESET and Dragos suggest involvement from a different Russian state-backed group known as Sandworm.
The attacks were purely destructive, with no ransom demand, and failed to disrupt electricity or heat supply. They highlight the growing risk of cyber sabotage in the energy sector and emphasize the need for increased awareness and preparedness among facilities operators and security experts.
**Key Findings:**
* Over 30 wind and solar farms, a manufacturing company, and a major heat and power plant were targeted. * The attacks aimed to cause disruption during severe winter weather but only impacted communications. * Electricity generation and heat supply were not interrupted. * Attackers used previously unknown wiper malware called DynoWiper and LazyWiper. * Analysis of the infrastructure used in the attack showed a high degree of overlap with Static Tundra.
**Recommendations:**
* Facilities operators must increase awareness and preparedness against cyber sabotage. * Regular security audits and penetration testing are essential to identify vulnerabilities. * Use multi-factor authentication and implement robust access controls. * Develop incident response plans to minimize the impact of attacks.